How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack
How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack
A Hack of Historic Proportions
On February 21, 2025, cryptocurrency exchange Bybit suffered the largest hack in crypto history—losing approximately $1.4–1.5 billion in ETH and ERC‑20 tokens from its cold wallet suite. The attackers, later attributed to North Korea’s Lazarus Group, deployed a counterfeit multisig interface to trick Bybit's custodians into approving a malicious transfer—then quickly laundered the stolen funds via decentralized exchanges and mixers.
Read QuantumGenie's other industry insights here.
Why Traditional Security Measures Fell Short
Bybit’s defenses included:
Multisig wallets: Thought secure due to multiple signatures—but the underlying SafeWallet interface was compromised.
Cold storage: Still vulnerable because the compromise occurred at the bridge between offline and online systems.
Audits and hardware security modules: These help—but don’t stop transaction-level manipulation once access is granted.
Repeated hacks across the crypto sector show that human and software vulnerabilities—not hardware—are often the weak points.
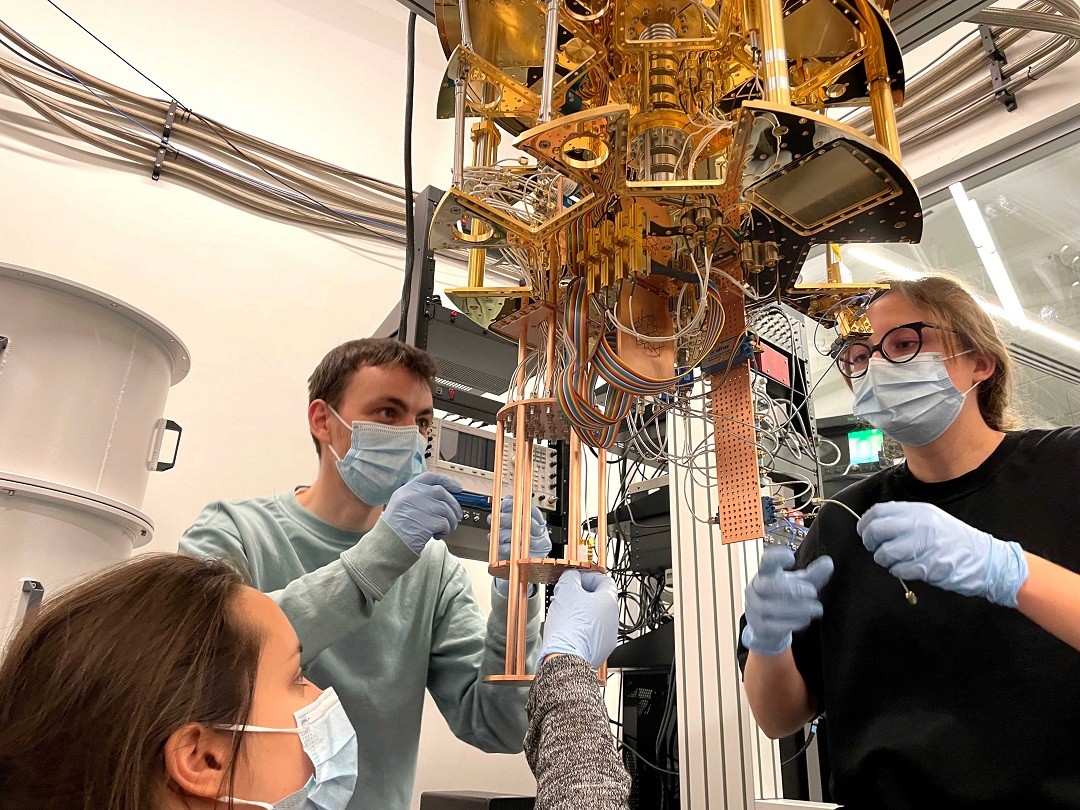
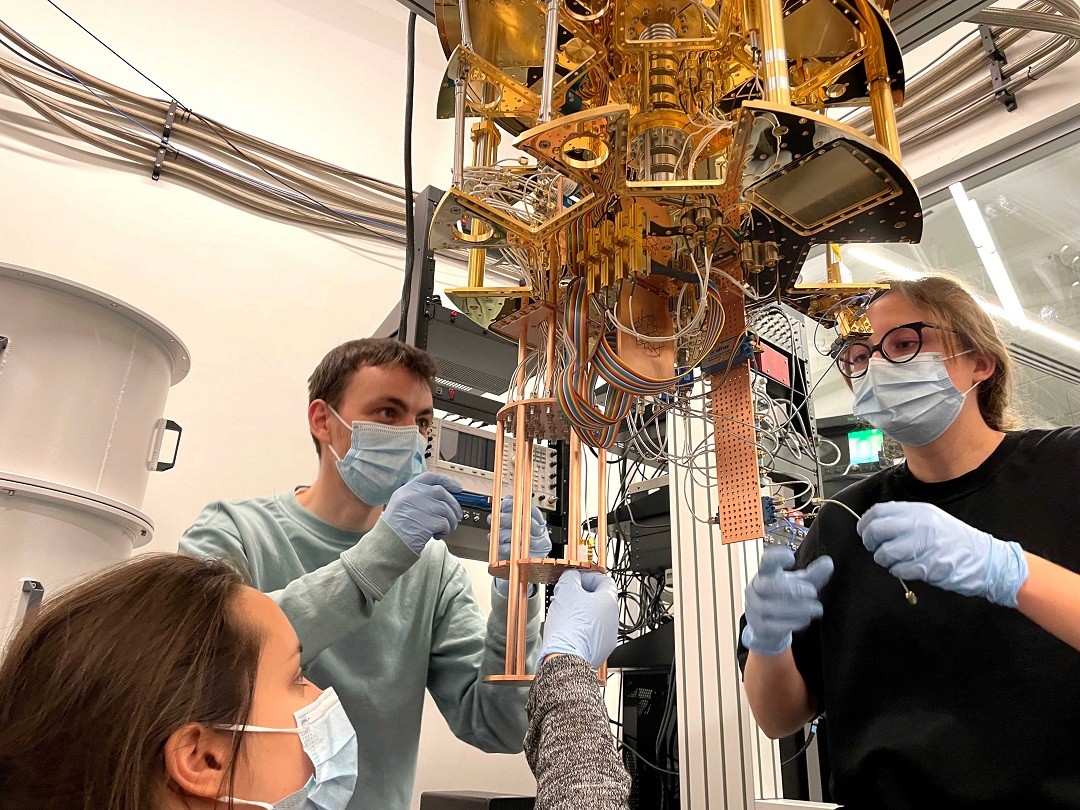
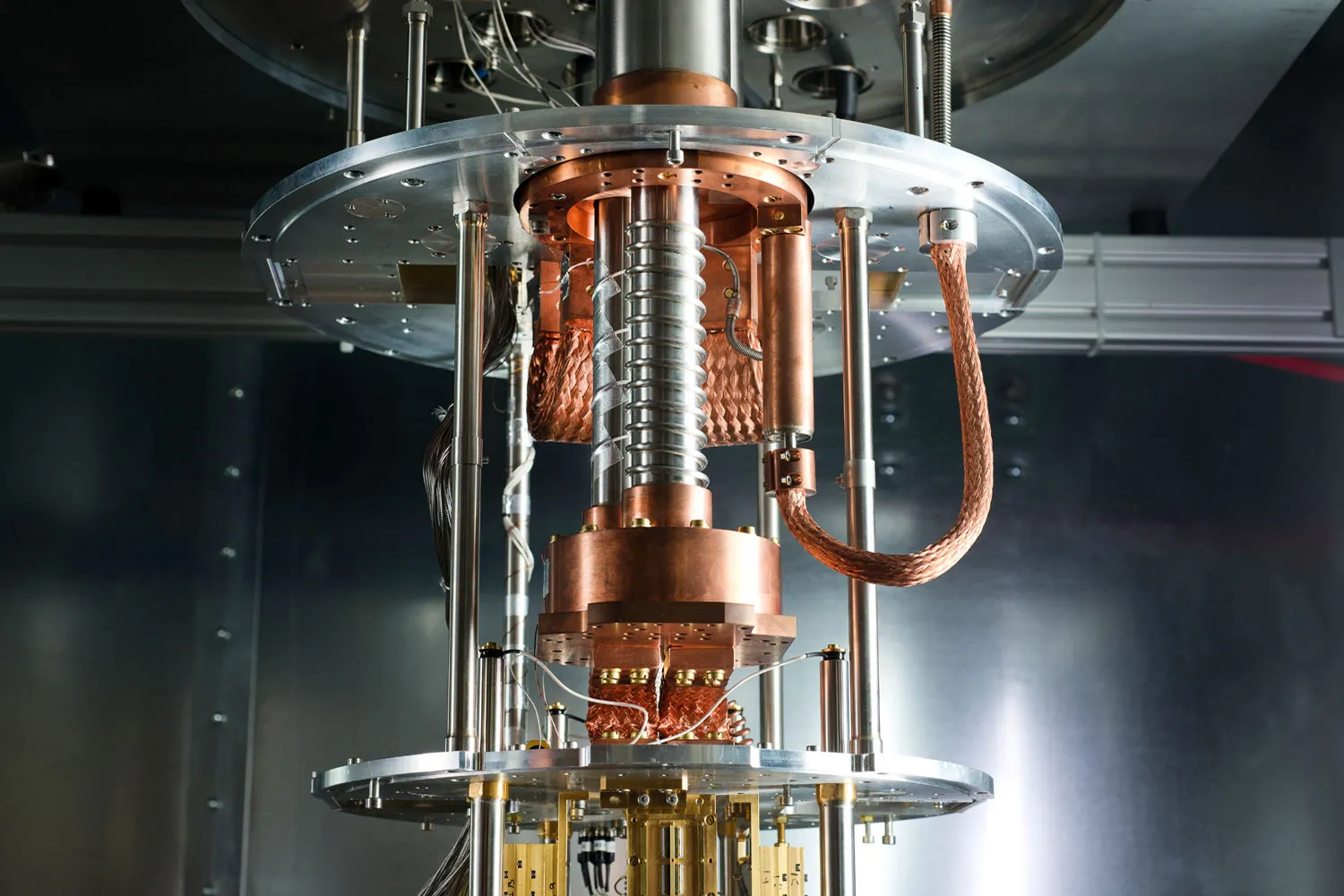
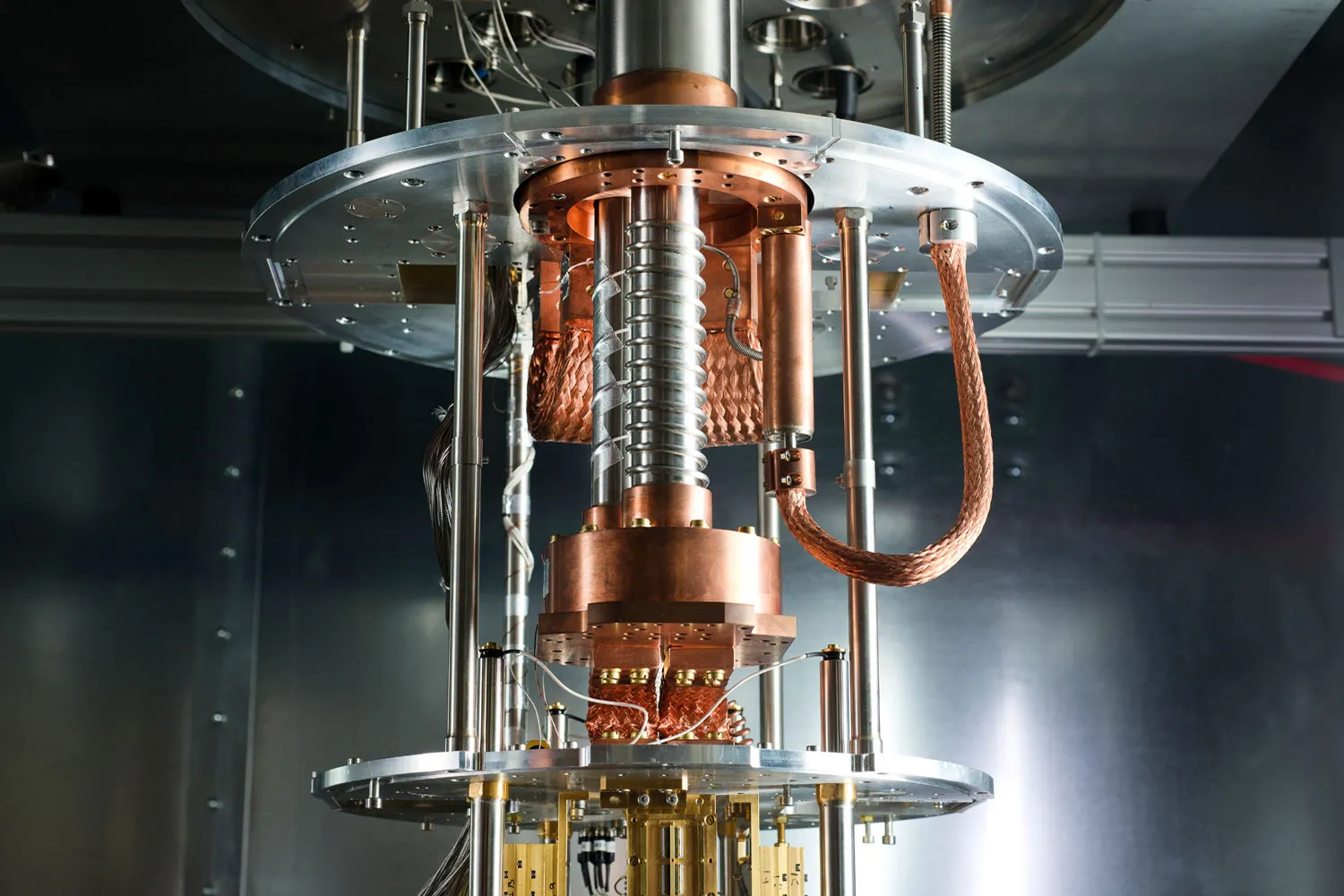
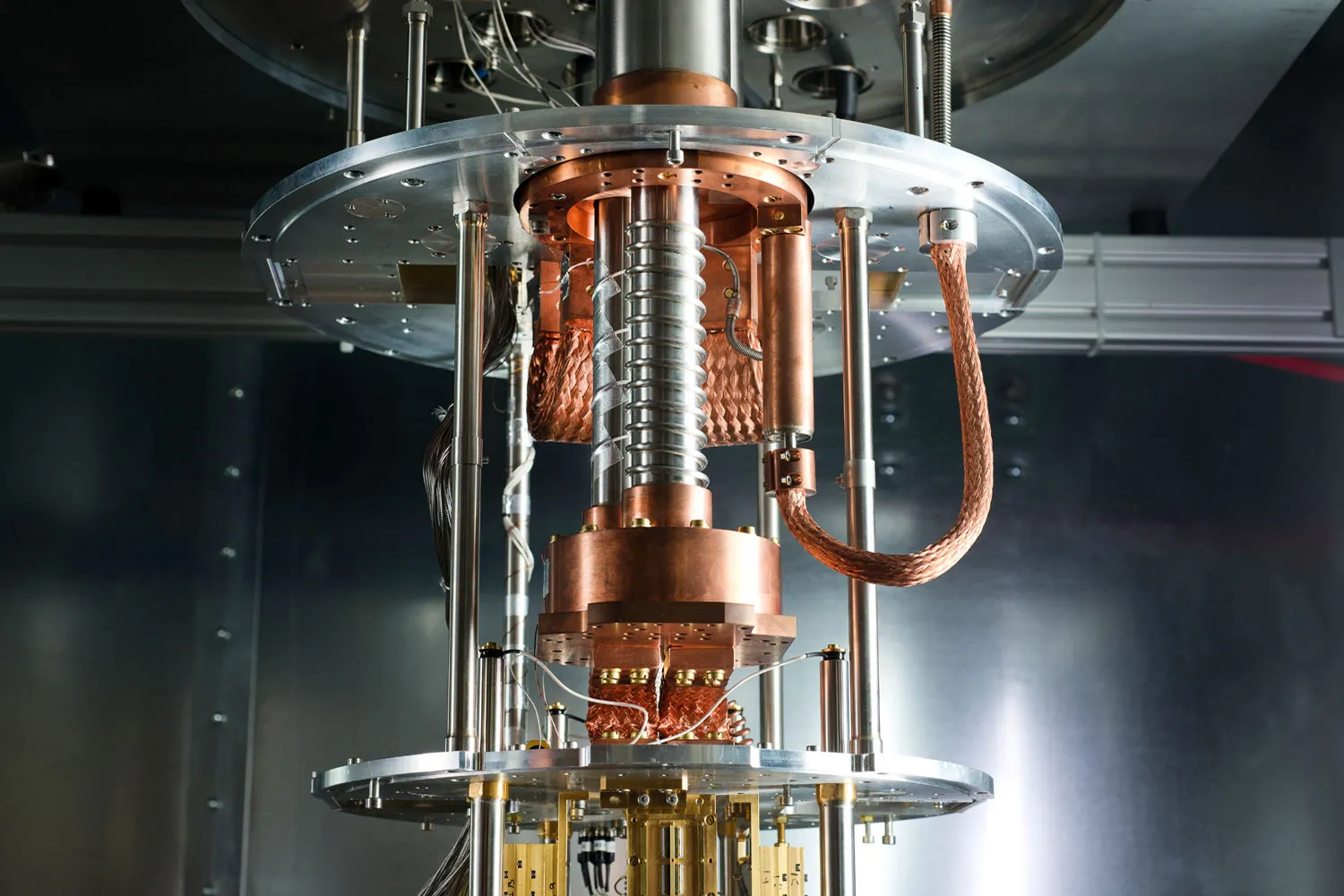
Enter Post-Quantum Cryptography (PQC)
Post-quantum cryptography comprises algorithms resistant to both classical and quantum-computer attacks, covering:
Digital signatures (e.g., CRYSTALS-Dilithium, SPHINCS+)
Key exchange/key encapsulation (e.g., CRYSTALS-Kyber)
PQC is designed for rigid authentication, stronger validation, and resistance to tampering—even in hostile environments.
Read QuantumGenie's other industry insights here.
How PQC Could Have Prevented or Mitigated the Breach
Unforgeable Multi-Signatures
PQC multi-signature schemes ensure all signers use quantum-secure keys. Even if the interface is compromised, fake transactions cannot pass cryptographic validation.Tamper-Resistant Transaction Signing
Utilizing quantum-resistant signature checks could enable automatic refusal of any out-of-policy or altered transaction—preventing unauthorized transfers.Safer Bridge Protocols
By securing the transfer process from cold to hot wallets with PQC, any tampering would be detected immediately, rejecting malicious commands.Enhanced Identity & Interface Security
PQC-based authentication across wallet UIs and APIs prevents spoofing or session hijacks, making remote interface compromises far less likely.
Real-World Protection: A Hypothetical Comparison
Attack PhaseWhat Happened (Bybit)What PQC Would DoInterface compromiseAttackers injected malicious UI to alter transactionPQC-based validation identifies tampering—rejects the requestSignature approvalSigners unknowingly approved malicious transactionPQC multi-sig prevents any invalid signature from passingFund transfer & laundering$1.4B drained & laundered via mixers and bridgesPQC doesn’t prevent laundering—but prevents the drain itself
While PQC does not eliminate laundering, it stops unauthorized transactions at the root—before funds leave the multisig wallet.
Read QuantumGenie's other industry insights here.
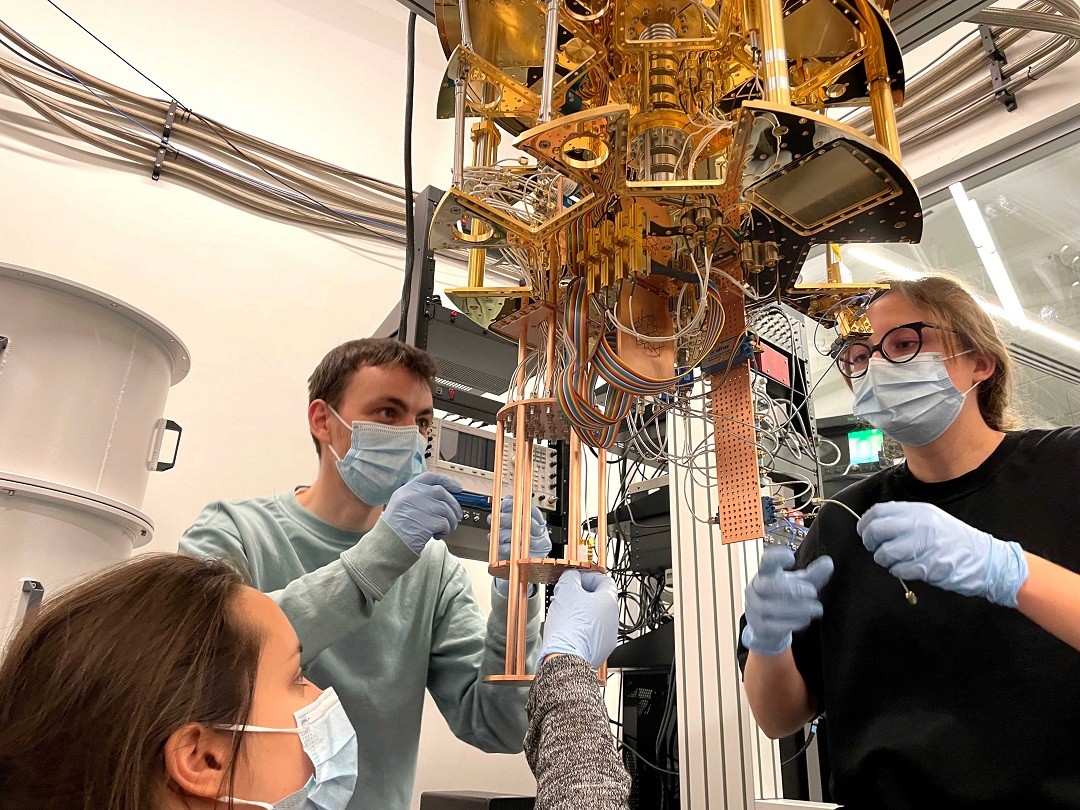
Beyond PQC: A Layered Defense Future
PQC should augment, not replace, current security infrastructure:
Zero-trust transaction verification
Real-time integrity checks with policy-aware logic
Rigorous audits + hardware and software tamper-resistance
By integrating PQC now, crypto platforms would vastly improve resistance to both human error and automated attack chains—while preparing for future quantum threats.
Conclusion: The Cost of Waiting is Too High
Bybit’s catastrophic loss serves as a sobering reminder: current defenses are insufficient. As crypto and finance ecosystems grow, so do threats—from cybercriminal syndicates today and quantum threats tomorrow.
Post-quantum cryptography isn't just about preparing for future quantum computers—it’s about fortifying systems against current, cunning adversaries. In a world where trust and transactions are digital, adopting PQC is not optional—it’s essential.
Quantum Insights
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack
Jul 21, 2025



Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire
Jul 20, 2025



Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Jul 17, 2025
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report
Jul 14, 2025



Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse
Jul 10, 2025



Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance
Jul 8, 2025



Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
Jun 26, 2025
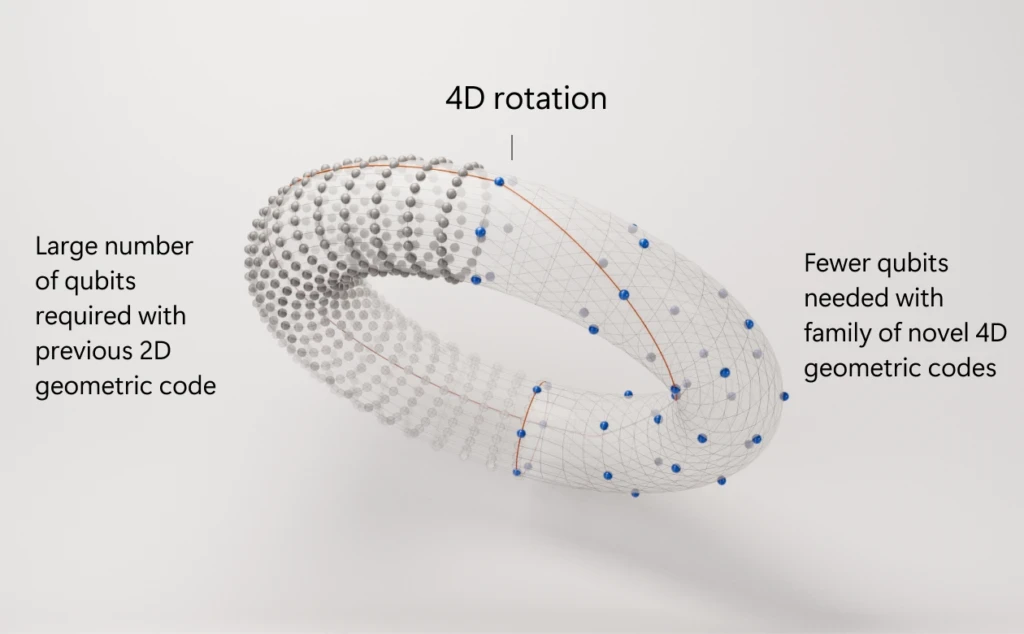
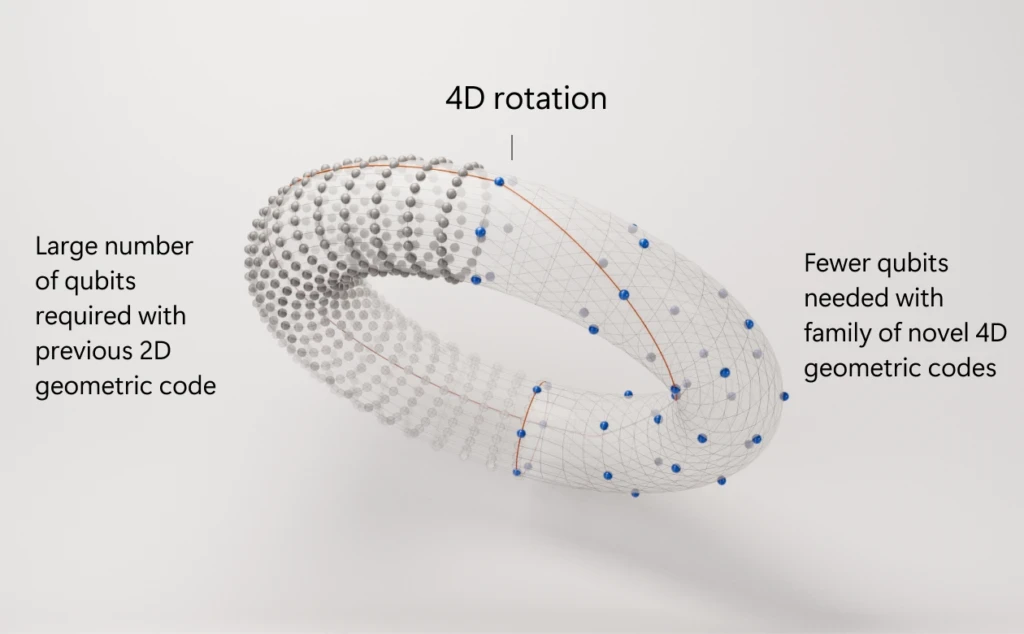
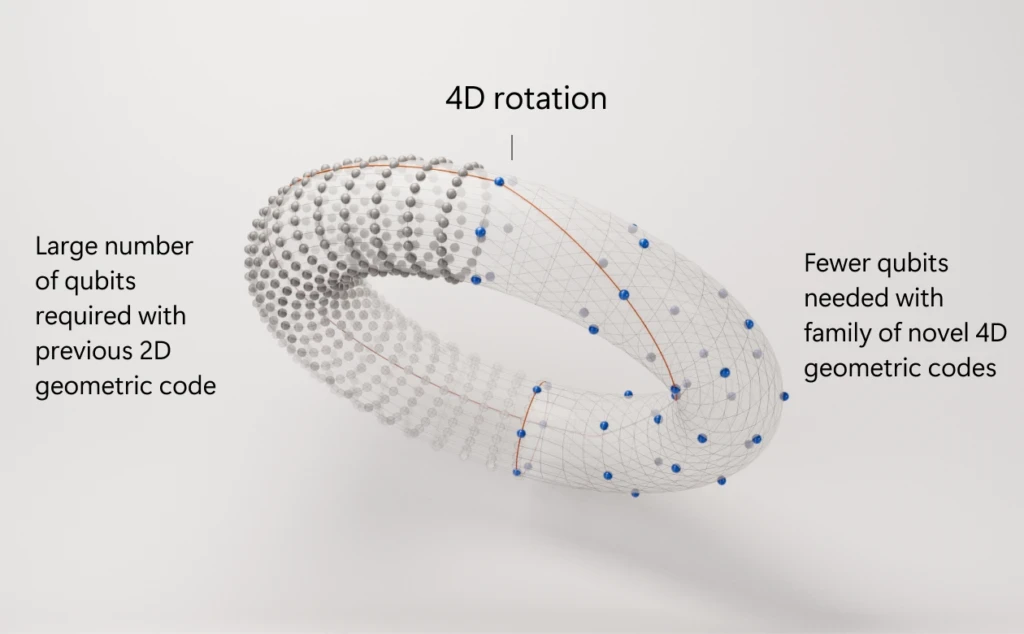
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors
Jun 22, 2025



How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack



IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer
Jun 18, 2025



Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence
Jun 17, 2025



Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025
Jun 15, 2025



Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing
Jun 12, 2025



Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’
Jun 11, 2024



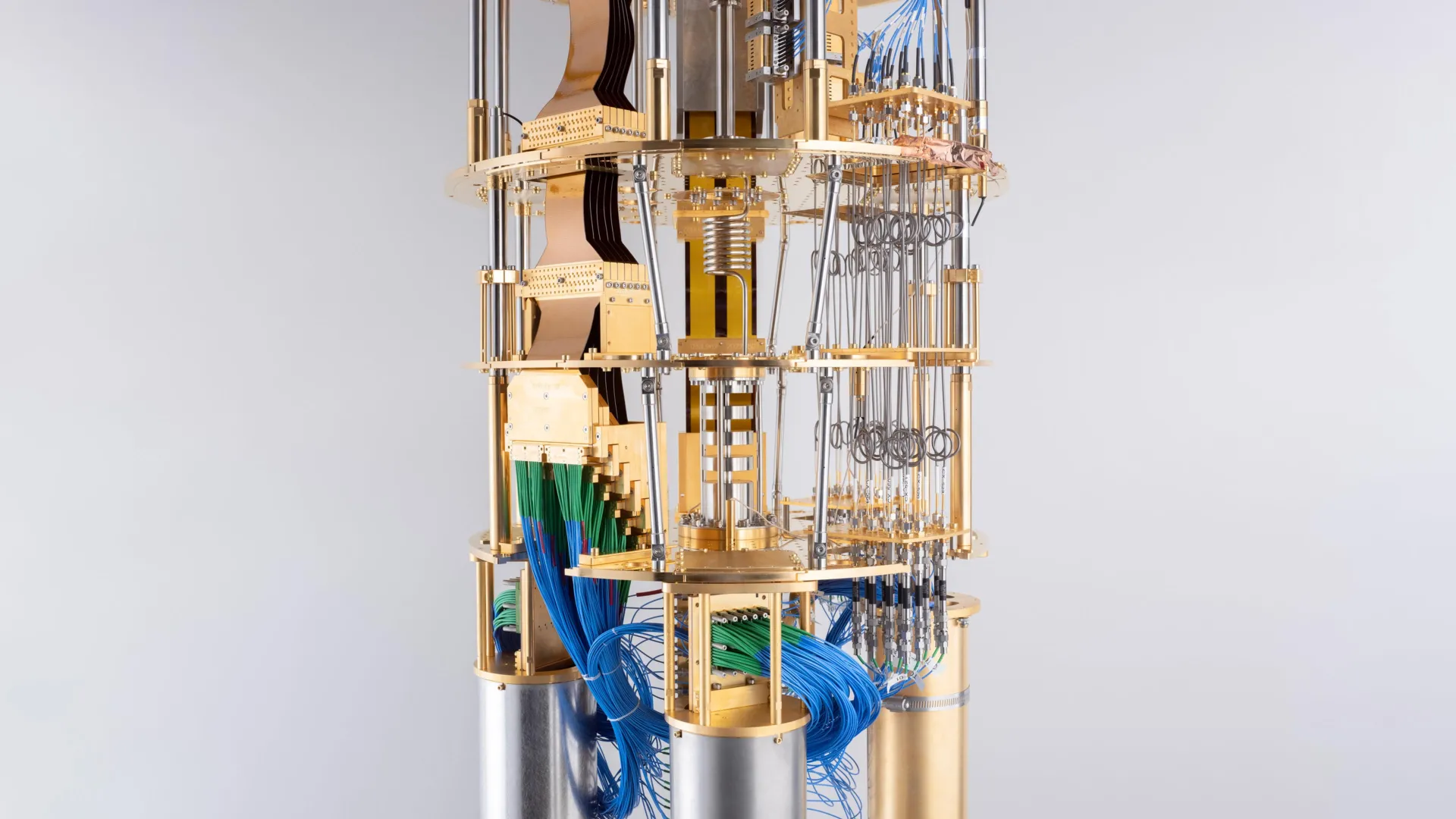
IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
Jun 10, 2025
IonQ Acquires Oxford Ionics for $1.08 Billion: A Bold Leap Toward Fault‑Tolerant Quantum Computing
Jun 9, 2025



Post‑Quantum Cryptography Takes Center Stage at Infosecurity Europe 2025
Jun 7, 2025



Oxford Quantum Circuits Unveils Bold Roadmap to 50,000 Logical Qubits by 2034
Jun 5, 2025



Caltech Achieves Hyper-Entanglement: A Quantum Breakthrough with Major Implications
Jun 5, 2025



Massive Data Breach Exposes Apple ID Logins: Why Post-Quantum Cryptography Must Start Now
Jun 4, 2025



A Quantum Celebration: UN Declares 2025 the International Year of Quantum Science and Technology
Jun 4, 2025



Crypto Asset Manager Grayscale Eyes the Quantum Frontier with Proposed Quantum Computing ETF
Jun 3, 2025
Quantum Entanglement: The Spooky Phenomenon That Could Transform Technology
Jun 2, 2025



Colt, Honeywell, and Nokia Launch Space-Based Trial for Quantum-Safe Cryptography
Jun 2, 2025



Surrogate Models Take Center Stage: A Smarter Way to Optimize Quantum Networks
May 31, 2025



Securing the Internet of Things: Why Post-Quantum Cryptography Is Critical for IoT's Future
May 30, 2025
Nord Quantique’s Multimode Qubit Breakthrough: A Leap Toward Scalable Quantum Computing
May 30, 2025
The 2025 Retail Cyberstorm: How Post-Quantum Cryptography Could Have Prevented Major Breaches
May 29, 2025



Microsoft’s Quantum Leap: Inside the Majorana Chip That Could Revolutionize Computing
May 29, 2025



Should Post-Quantum Cryptography Start Now? The Clock Is Ticking
May 28, 2025



Cracking RSA with Fewer Qubits: What Google's New Quantum Factoring Estimate Means for Cybersecurity
May 28, 2025



Quantum Arms Race: U.S. Defense Intelligence Flags Rivals’ Growing Military Use of Quantum Tech
May 27, 2025



Quantum Threats and Bitcoin: Why BlackRock’s Warning Matters for the Future of Crypto Security
May 27, 2025



Sudbury's SNOLAB Ventures into Quantum Computing Research
May 26, 2025
Lockheed Martin and IBM Pioneer Quantum-Classical Hybrid Computing for Complex Molecular Simulations
May 23, 2025



Why the Moon Matters for Quantum Computing: From Helium-3 to Off-Planet Quantum Networks
May 23, 2025



NIST Approves Three Post-Quantum Cryptography Standards: A Milestone for Digital Security
May 22, 2025



Scientists Connect Quantum Processors via Fiber Optic Cable for the First Time
May 21, 2025



Quantum Computing and Encryption Breakthroughs in 2025: A New Era of Innovation
May 21, 2025



How CISOs Can Defend Against the “Harvest Now, Decrypt Later” Threat
May 20, 2025



NVIDIA Expands Quantum and AI Ecosystem in Taiwan Through Strategic Partnerships and Supercomputing Initiatives
May 19, 2025



Quantum Annealing Breakthrough: Quantum Computer Outperforms Fastest Supercomputers
May 18, 2025



Quantum Computing's New Frontier: How the $1.4 Trillion US–UAE Investment Deal is Shaping the Industry
May 16, 2025



Quantum Computing Meets Cancer Research: A New Frontier in Drug Discovery
May 16, 2025



Quantum Industry Leaders Urge Congress to Reauthorize and Expand National Quantum Initiative
May 15, 2025



Honeywell's Quantinuum and Qatar's Al Rabban Capital Forge $1 Billion Quantum Computing Joint Venture
May 15, 2025



Advancing Quantum Machine Learning with Multi-Chip Ensemble Architectures
May 14, 2025



How will the new US-Saudi Arabia AI deal effect the Quantum Computing industry?
May 14, 2025



Saudi Arabia's $600 Billion AI Push: Amazon, Nvidia, and Global Tech Giants Lead the Charge
May 14, 2025



Quantum Computing Breakthrough: Diamond Qubits Achieve Unprecedented Precision
Apr 28, 2025



Australia’s Quantum Cryptography Roadmap: Preparing for a Post-Quantum Future
Apr 26, 2025



Harvest Now, Decrypt later
Apr 25, 2025



NIST’s New Quantum Cryptography Standards: What You Need to Know
Apr 25, 2025
Read our latest commentary and research on the post-quantum encryption space
Read our latest commentary and research on the post-quantum encryption space
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack


Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire


Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report


Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse


Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance


Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
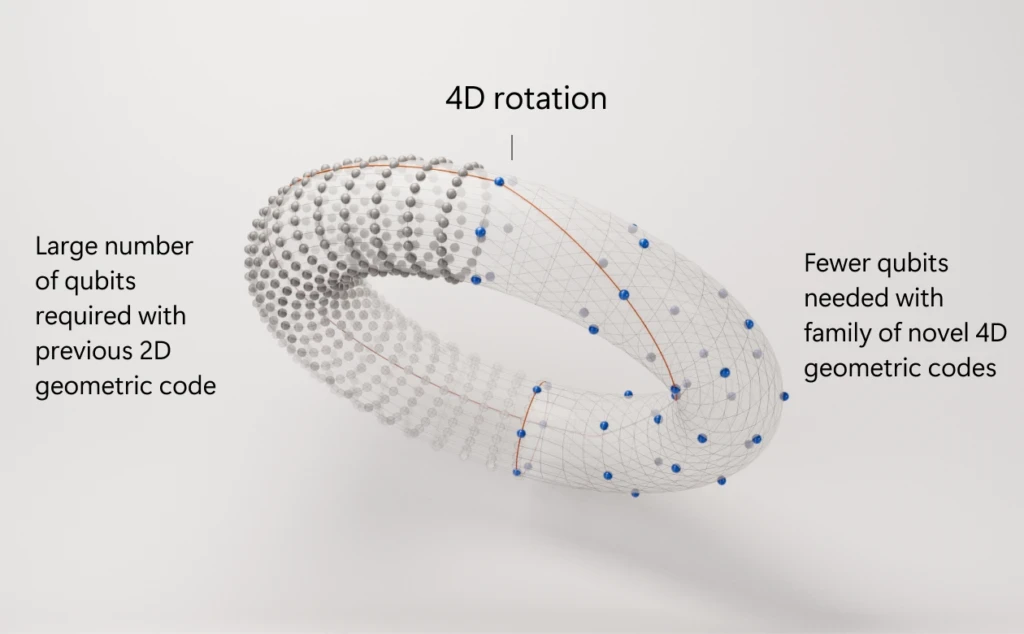
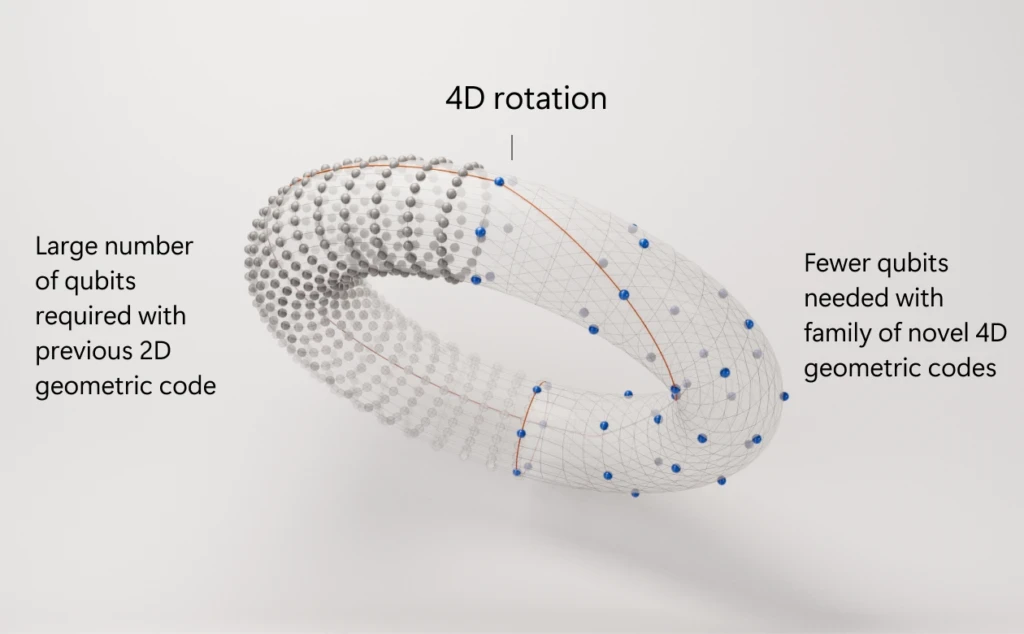
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors


How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack


IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer


Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence


Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025


Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing


Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’


IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack

Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire

Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report

Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse

Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance

Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
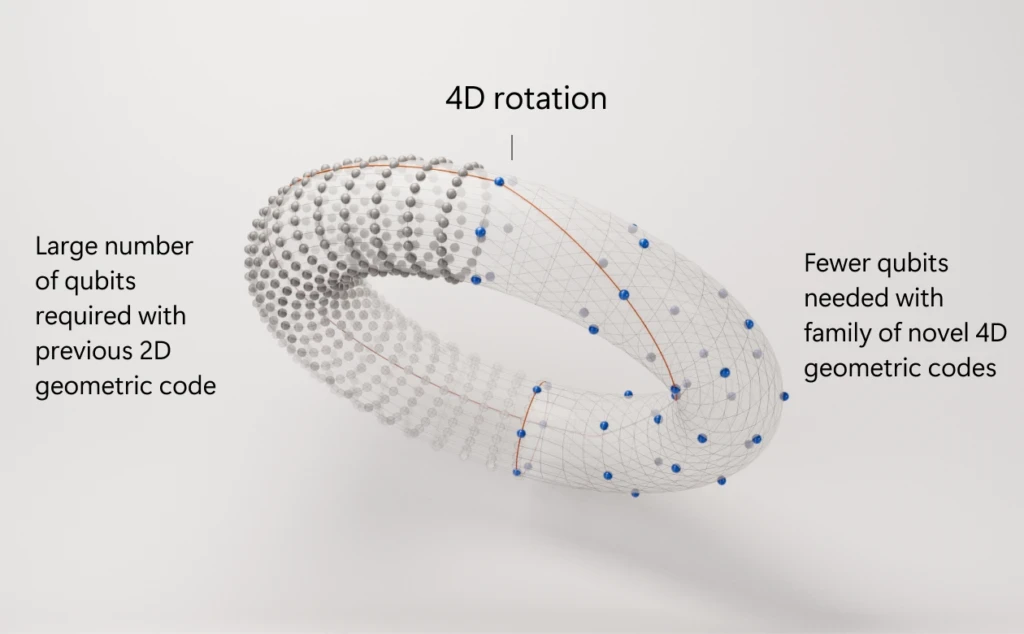
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors

How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack

IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer

Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence

Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025

Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing

Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’

IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
A Hack of Historic Proportions
On February 21, 2025, cryptocurrency exchange Bybit suffered the largest hack in crypto history—losing approximately $1.4–1.5 billion in ETH and ERC‑20 tokens from its cold wallet suite. The attackers, later attributed to North Korea’s Lazarus Group, deployed a counterfeit multisig interface to trick Bybit's custodians into approving a malicious transfer—then quickly laundered the stolen funds via decentralized exchanges and mixers.
Read QuantumGenie's other industry insights here.
Why Traditional Security Measures Fell Short
Bybit’s defenses included:
Multisig wallets: Thought secure due to multiple signatures—but the underlying SafeWallet interface was compromised.
Cold storage: Still vulnerable because the compromise occurred at the bridge between offline and online systems.
Audits and hardware security modules: These help—but don’t stop transaction-level manipulation once access is granted.
Repeated hacks across the crypto sector show that human and software vulnerabilities—not hardware—are often the weak points.
Enter Post-Quantum Cryptography (PQC)
Post-quantum cryptography comprises algorithms resistant to both classical and quantum-computer attacks, covering:
Digital signatures (e.g., CRYSTALS-Dilithium, SPHINCS+)
Key exchange/key encapsulation (e.g., CRYSTALS-Kyber)
PQC is designed for rigid authentication, stronger validation, and resistance to tampering—even in hostile environments.
Read QuantumGenie's other industry insights here.
How PQC Could Have Prevented or Mitigated the Breach
Unforgeable Multi-Signatures
PQC multi-signature schemes ensure all signers use quantum-secure keys. Even if the interface is compromised, fake transactions cannot pass cryptographic validation.Tamper-Resistant Transaction Signing
Utilizing quantum-resistant signature checks could enable automatic refusal of any out-of-policy or altered transaction—preventing unauthorized transfers.Safer Bridge Protocols
By securing the transfer process from cold to hot wallets with PQC, any tampering would be detected immediately, rejecting malicious commands.Enhanced Identity & Interface Security
PQC-based authentication across wallet UIs and APIs prevents spoofing or session hijacks, making remote interface compromises far less likely.
Real-World Protection: A Hypothetical Comparison
Attack PhaseWhat Happened (Bybit)What PQC Would DoInterface compromiseAttackers injected malicious UI to alter transactionPQC-based validation identifies tampering—rejects the requestSignature approvalSigners unknowingly approved malicious transactionPQC multi-sig prevents any invalid signature from passingFund transfer & laundering$1.4B drained & laundered via mixers and bridgesPQC doesn’t prevent laundering—but prevents the drain itself
While PQC does not eliminate laundering, it stops unauthorized transactions at the root—before funds leave the multisig wallet.
Read QuantumGenie's other industry insights here.
Beyond PQC: A Layered Defense Future
PQC should augment, not replace, current security infrastructure:
Zero-trust transaction verification
Real-time integrity checks with policy-aware logic
Rigorous audits + hardware and software tamper-resistance
By integrating PQC now, crypto platforms would vastly improve resistance to both human error and automated attack chains—while preparing for future quantum threats.
Conclusion: The Cost of Waiting is Too High
Bybit’s catastrophic loss serves as a sobering reminder: current defenses are insufficient. As crypto and finance ecosystems grow, so do threats—from cybercriminal syndicates today and quantum threats tomorrow.
Post-quantum cryptography isn't just about preparing for future quantum computers—it’s about fortifying systems against current, cunning adversaries. In a world where trust and transactions are digital, adopting PQC is not optional—it’s essential.
Let's talk!
Office:
1535 Broadway
New York, NY 10036
USA
Local time:
00:43:30
Let's talk!
Office:
1535 Broadway
New York, NY 10036
USA
Local time:
00:43:30
