Harvest Now, Decrypt later
Harvest Now, Decrypt later
April 25, 2025
"Harvest Now, Decrypt Later": The Quiet Threat to Data Security
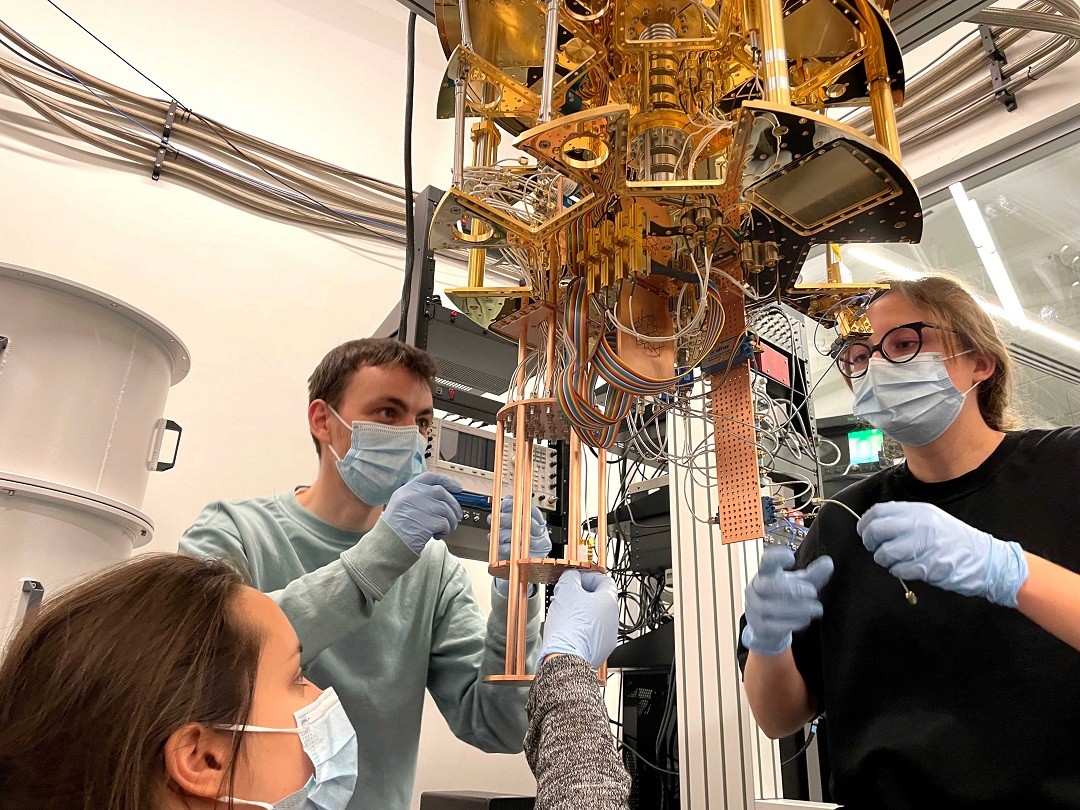
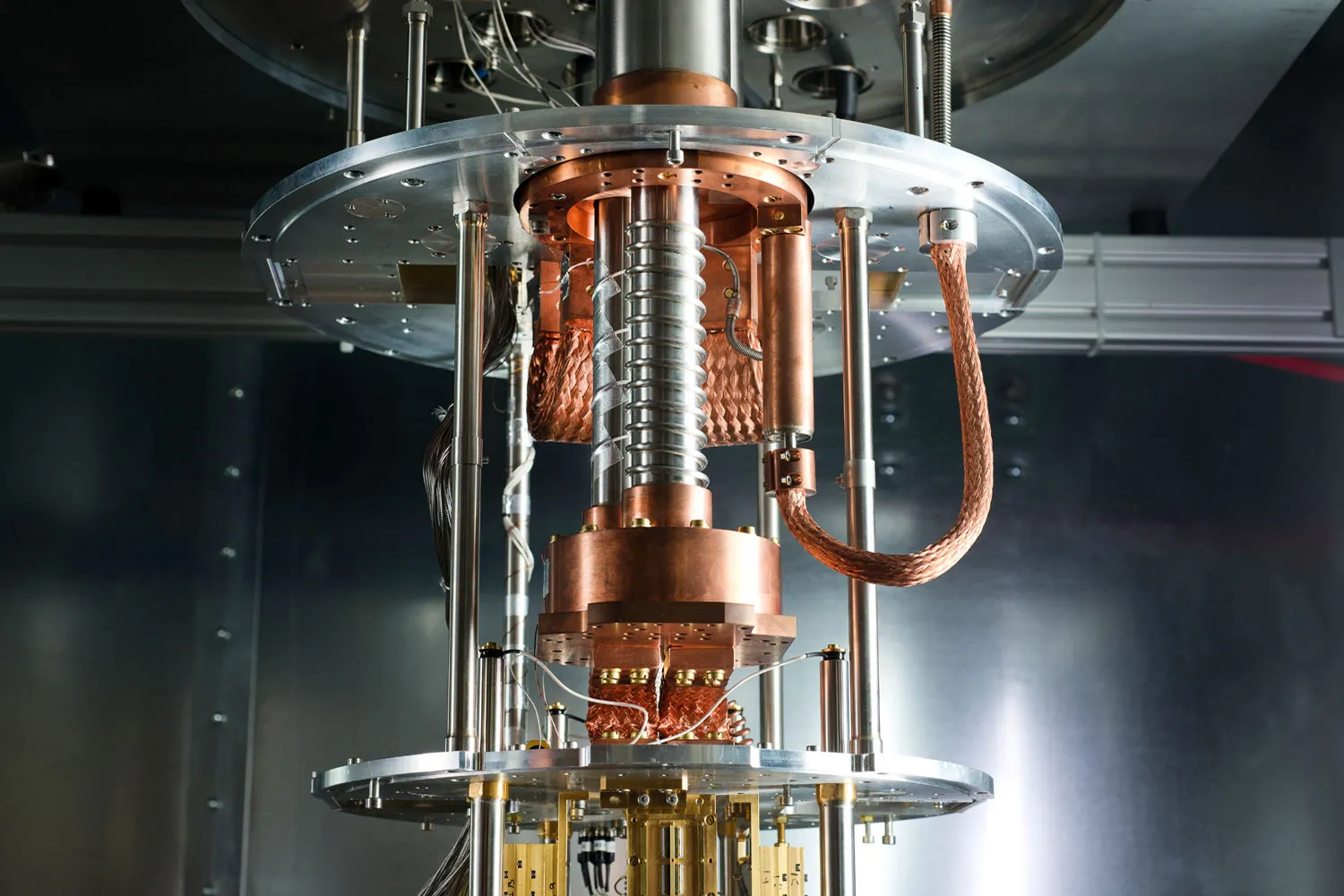
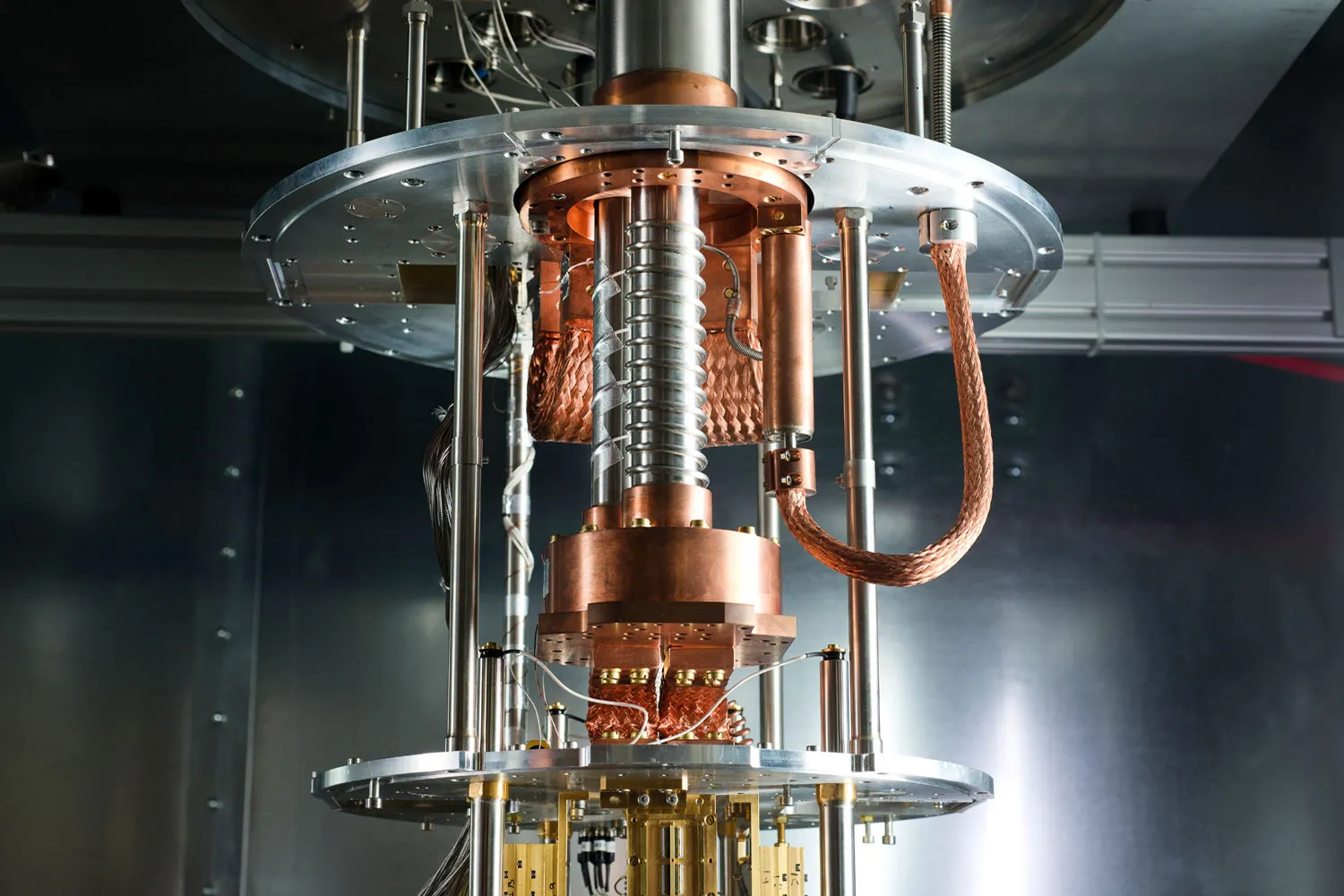
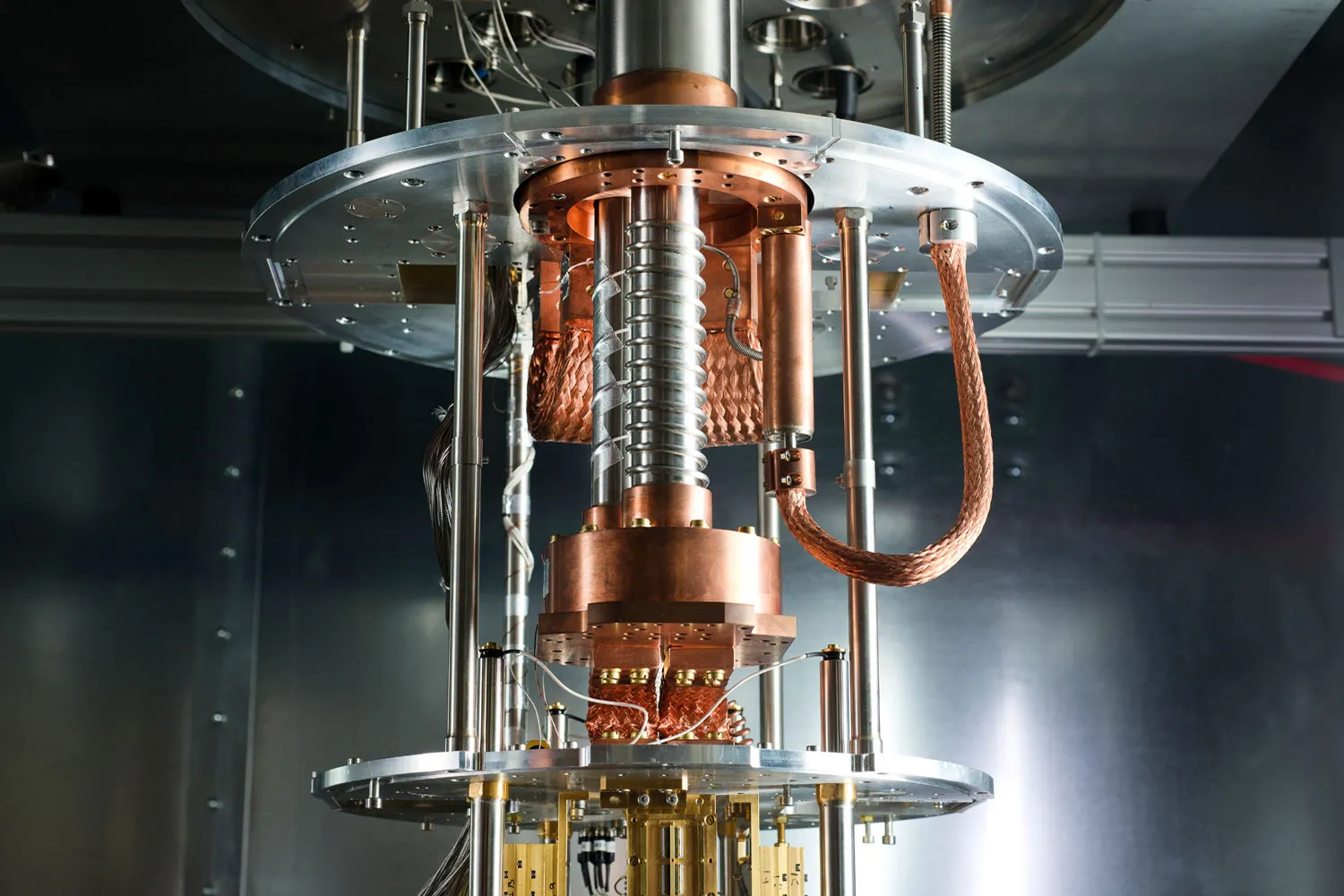
In the ever-evolving world of cybersecurity, one looming threat has experts particularly concerned: "Harvest Now, Decrypt Later" (HNDL) attacks. While the name might sound like a sci-fi subplot, the concept is simple and the danger is very real—especially as quantum computing moves from theory to reality.
What Is "Harvest Now, Decrypt Later"?
A "Harvest Now, Decrypt Later" strategy refers to a long-term cyberattack where a malicious actor intercepts and stores encrypted data today with the intent of decrypting it in the future when more powerful computing—especially quantum computers—can break current encryption standards.
In simpler terms, it’s like stealing a locked safe today, knowing you don’t have the key but betting that one day you'll have the lock-picking tools needed to open it.
Why Is This a Big Deal?
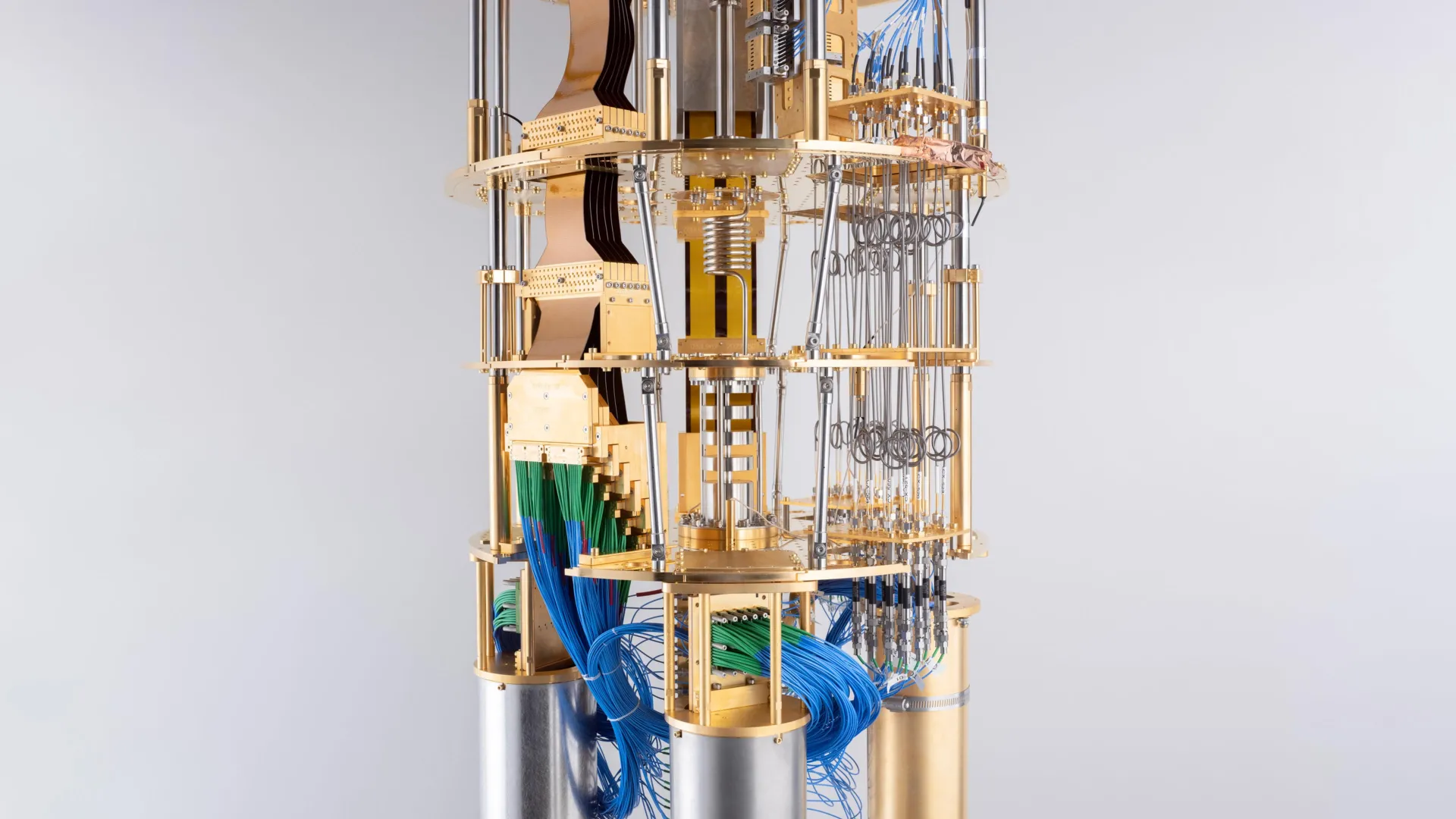
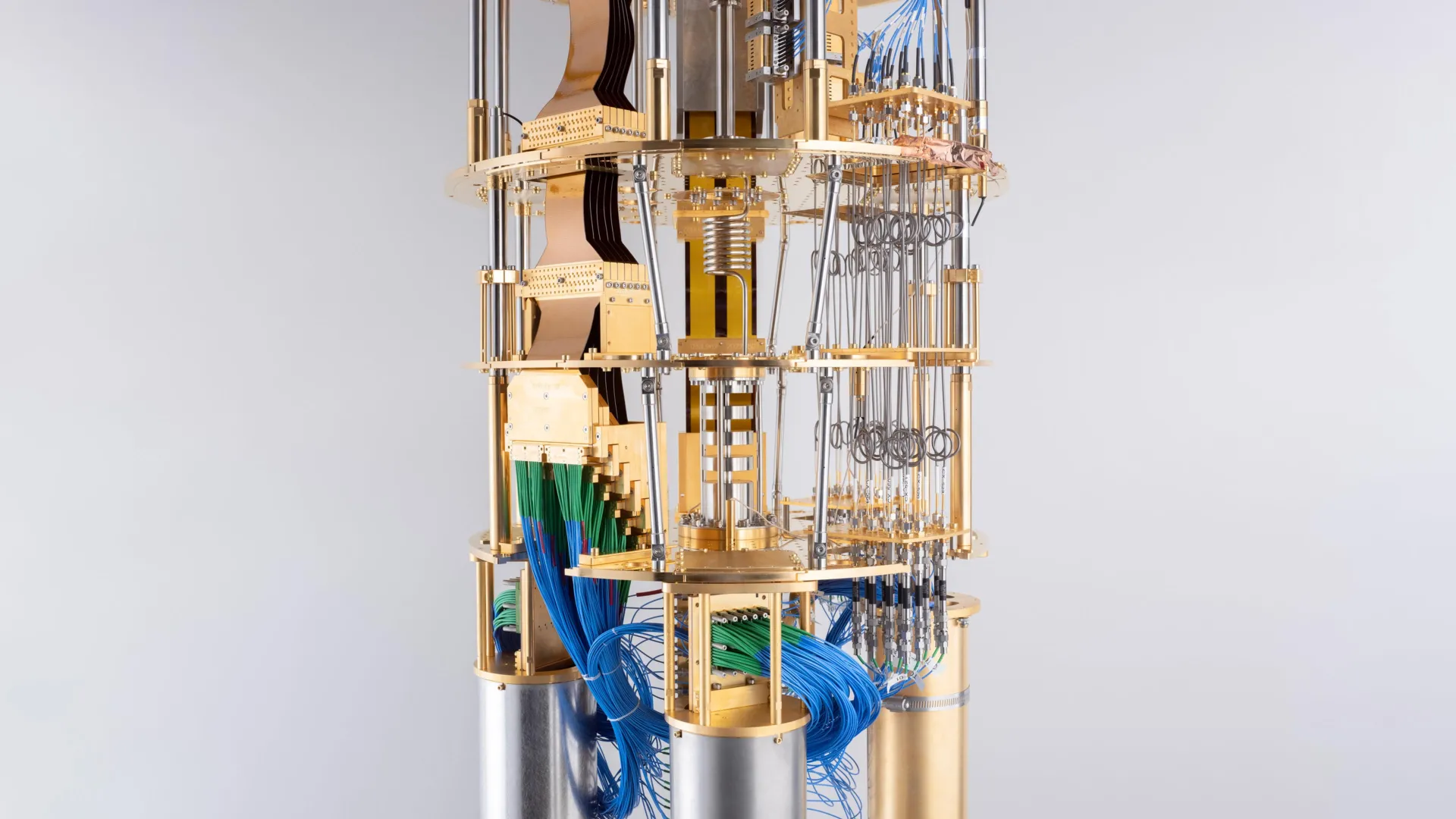
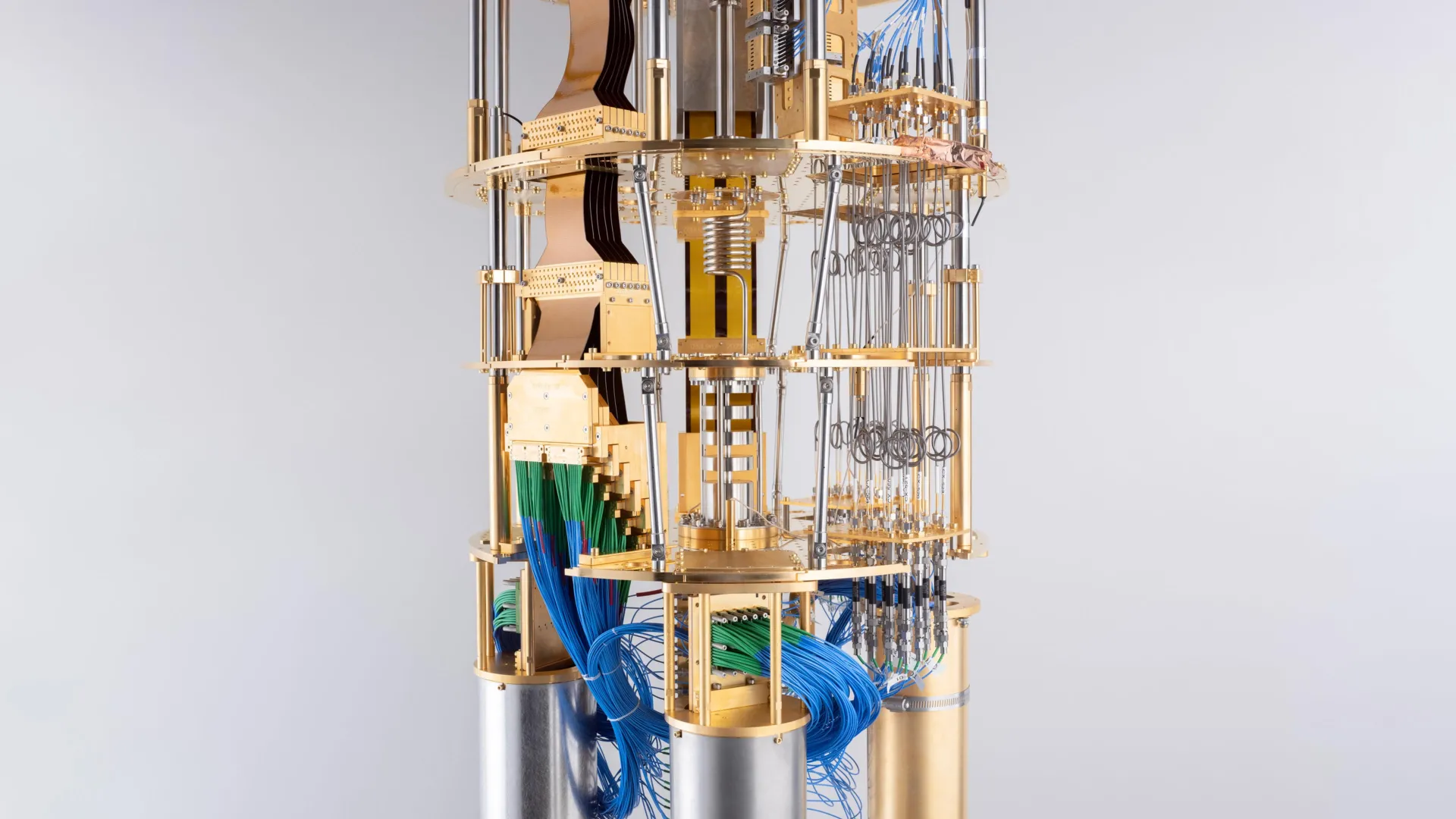
Most of the world’s sensitive data—banking information, medical records, government communications, intellectual property—is protected by encryption standards like RSA, ECC, and AES. These encryption systems are strong against traditional computers but could be broken relatively easily by future quantum computers using algorithms like Shor’s algorithm or Grover’s algorithm.
This creates a dangerous mismatch: data that is encrypted securely today could become fully exposed tomorrow. And by "tomorrow," we mean a future that could be just 5 to 15 years away, depending on the pace of quantum advancements.
What Kind of Data Is at Risk?
Not all data has the same shelf life. Some data becomes irrelevant within hours, while other information remains sensitive for decades. Here are some prime targets for HNDL attacks:
Military and diplomatic communications
Healthcare and genetic data
Corporate trade secrets
Research and development blueprints
Financial records
User credentials
In short: anything that could still be valuable or damaging in the future is fair game.
Who’s Doing This?
While specific actors are hard to identify, experts believe that nation-states with the resources to develop quantum technologies (such as the U.S., China, and Russia) are the most likely candidates to be engaging in "Harvest Now, Decrypt Later" operations.
These attacks are attractive because they can be carried out covertly. A spy agency doesn’t need to break into a network; they just need to passively tap into communication lines, download encrypted traffic, and store it for the long haul.
What Can Be Done About It?
This threat is already being taken seriously. The cybersecurity community is actively working on a new generation of cryptographic algorithms known as Post-Quantum Cryptography (PQC)—encryption methods that are designed to withstand the immense power of quantum computing.
Organizations like the National Institute of Standards and Technology (NIST) have been leading efforts to standardize post-quantum cryptographic algorithms. In 2022, NIST announced its initial selections for quantum-resistant encryption, which are now being prepared for widespread adoption.
Steps You Can Take Now
While we wait for quantum computers to mature, there are several proactive steps that individuals and organizations can take:
Audit your data: Identify which data has long-term confidentiality requirements.
Adopt crypto agility: Design systems that can easily switch to new encryption algorithms.
Start experimenting with post-quantum solutions: Pilot PQC options and stay informed on NIST’s progress.
Monitor for suspicious activity: Just because someone can’t decrypt traffic today doesn’t mean they aren’t harvesting it.
Educate your team: Make sure your cybersecurity professionals are aware of quantum threats and future-proofing strategies.
Final Thoughts
“Harvest Now, Decrypt Later” is a quiet, patient form of cyber-espionage that bets on the future. And with quantum computing advancing rapidly, that future might be closer than we think. If organizations don’t begin to prepare now, they may find themselves caught off-guard when yesterday’s stolen secrets become tomorrow’s biggest security breach.
Quantum-safe security isn’t just a buzzword—it’s becoming a necessity.
April 25, 2025
Quantum Insights
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack
Jul 21, 2025



Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire
Jul 20, 2025



Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Jul 17, 2025
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report
Jul 14, 2025



Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse
Jul 10, 2025



Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance
Jul 8, 2025



Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
Jun 26, 2025
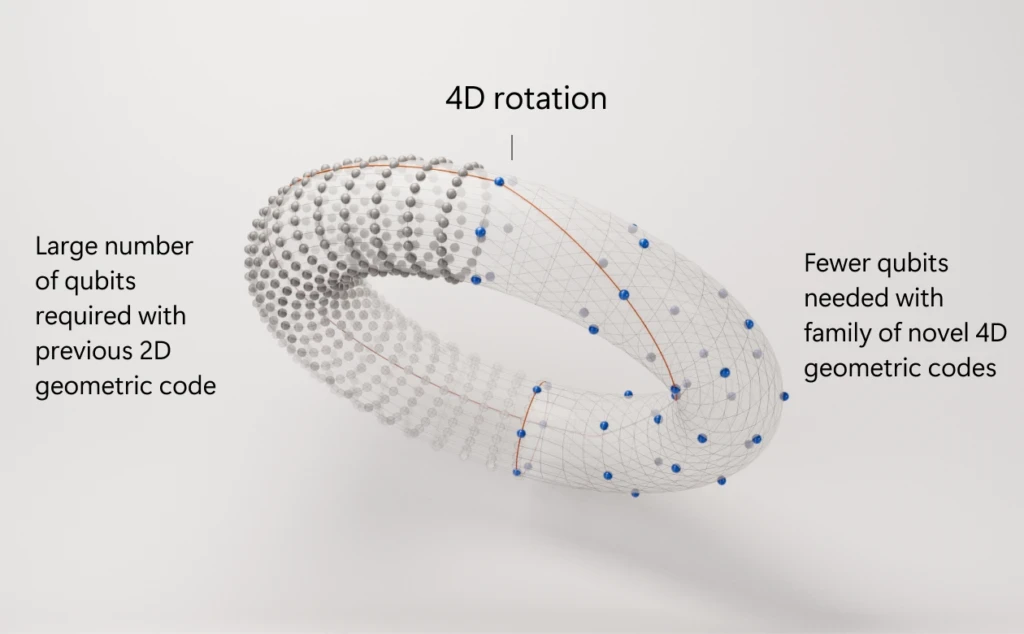
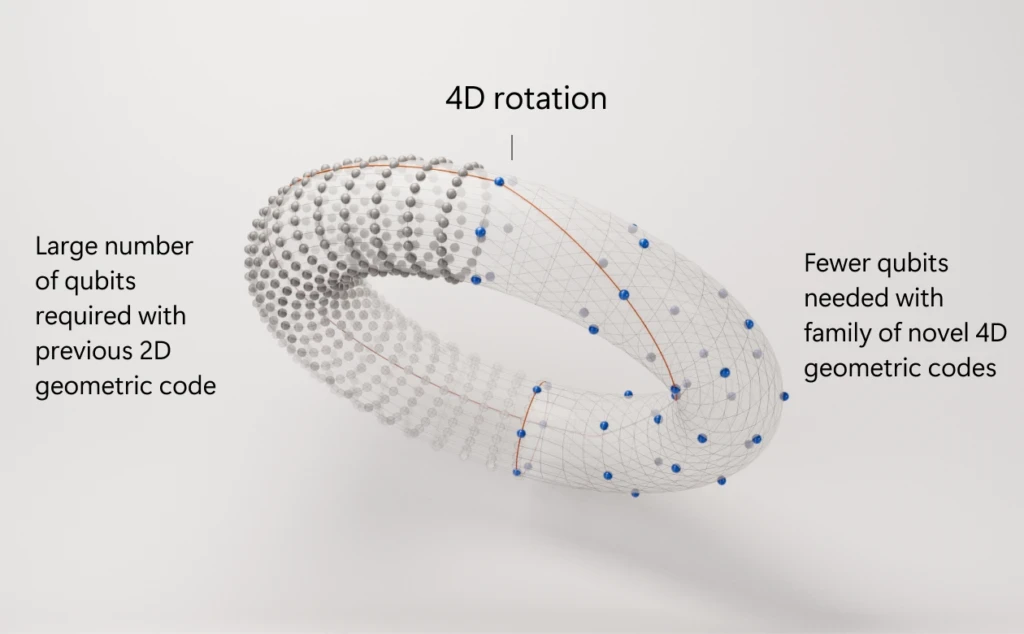
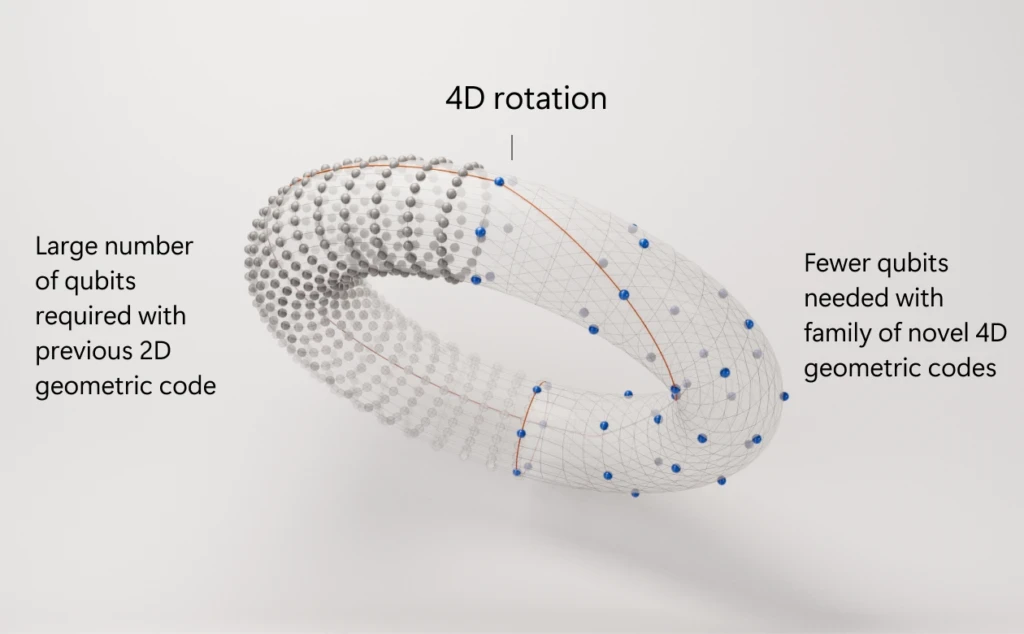
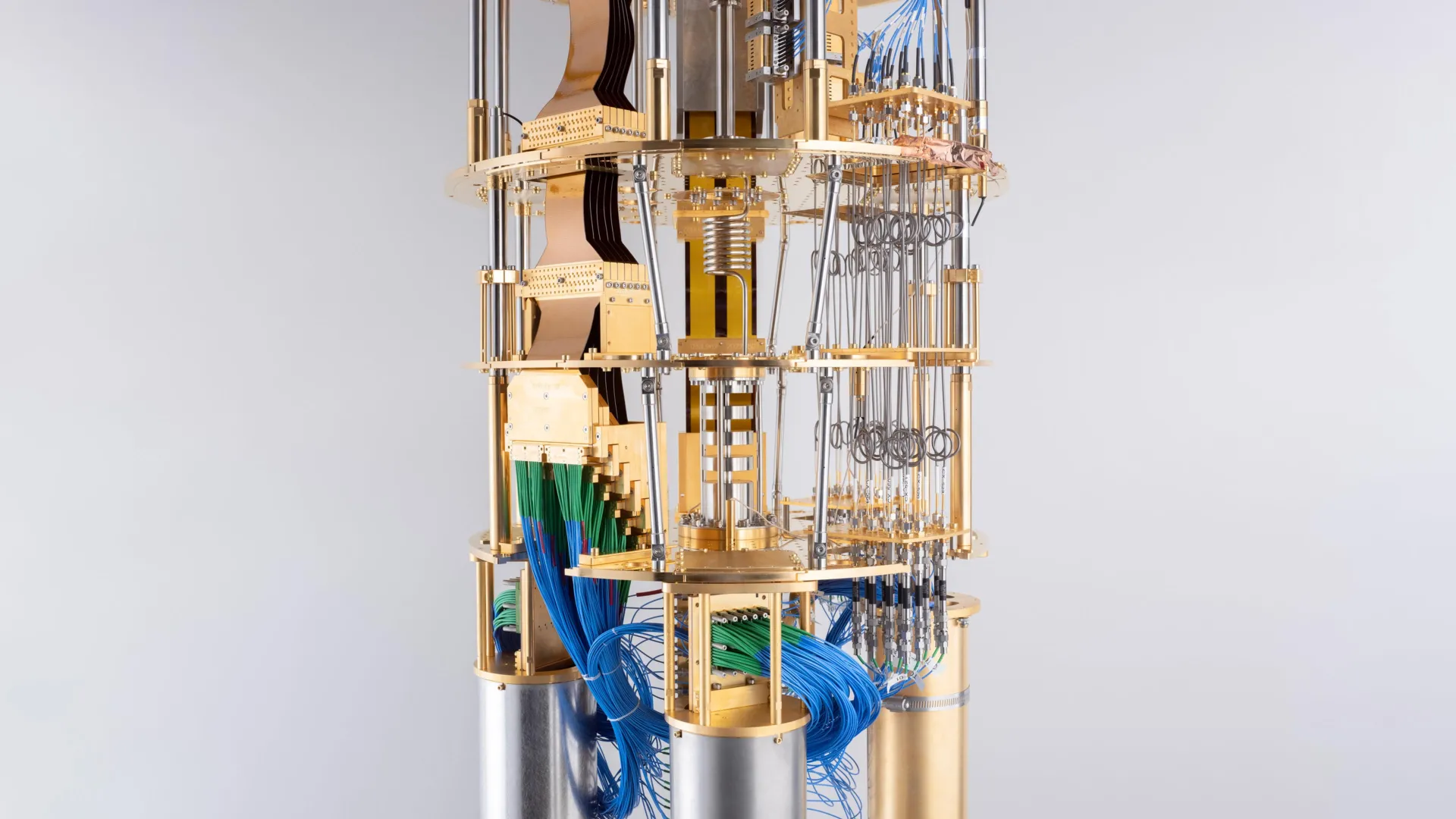
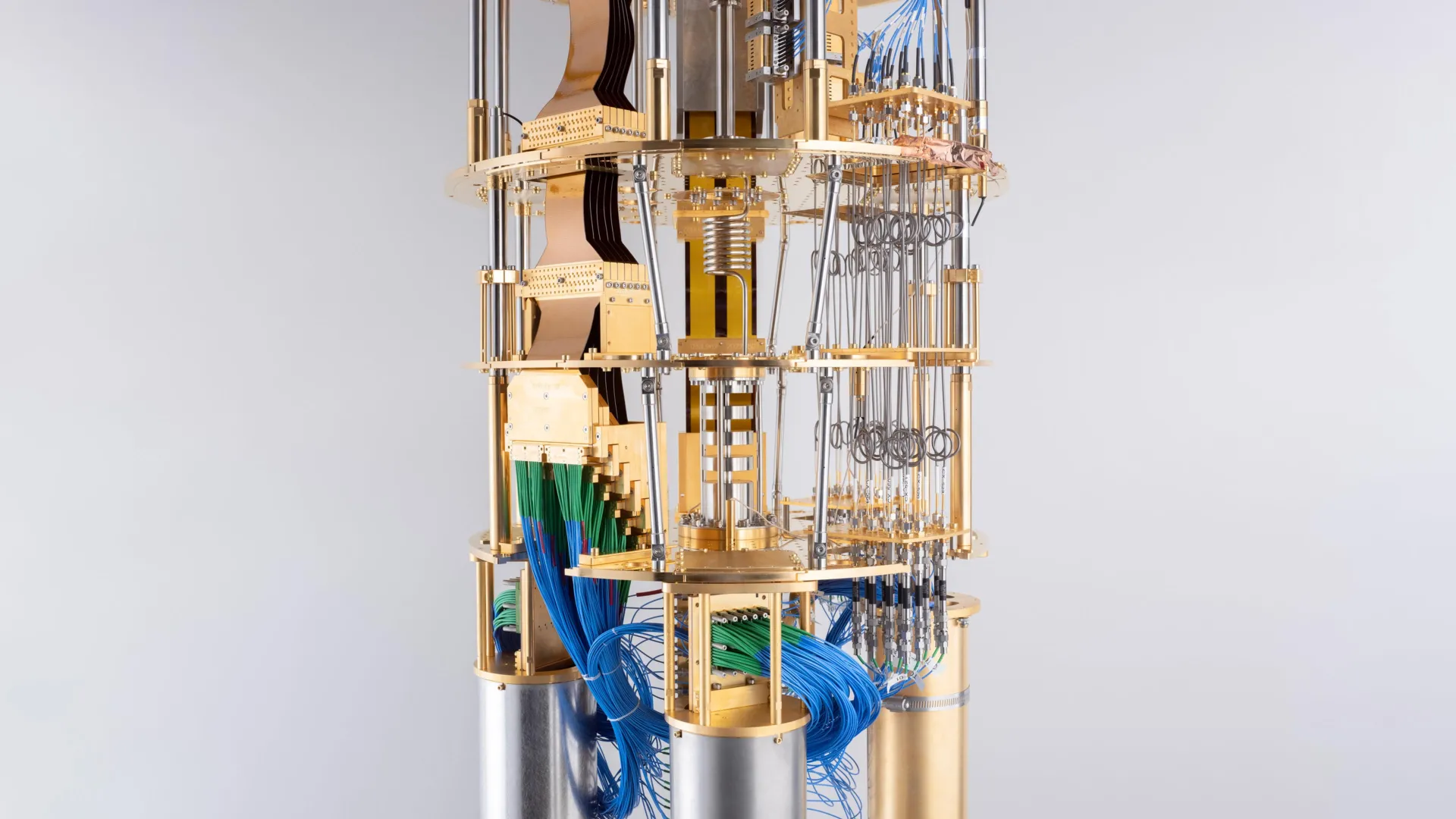
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors
Jun 22, 2025



How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack



IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer
Jun 18, 2025



Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence
Jun 17, 2025



Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025
Jun 15, 2025



Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing
Jun 12, 2025



Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’
Jun 11, 2024



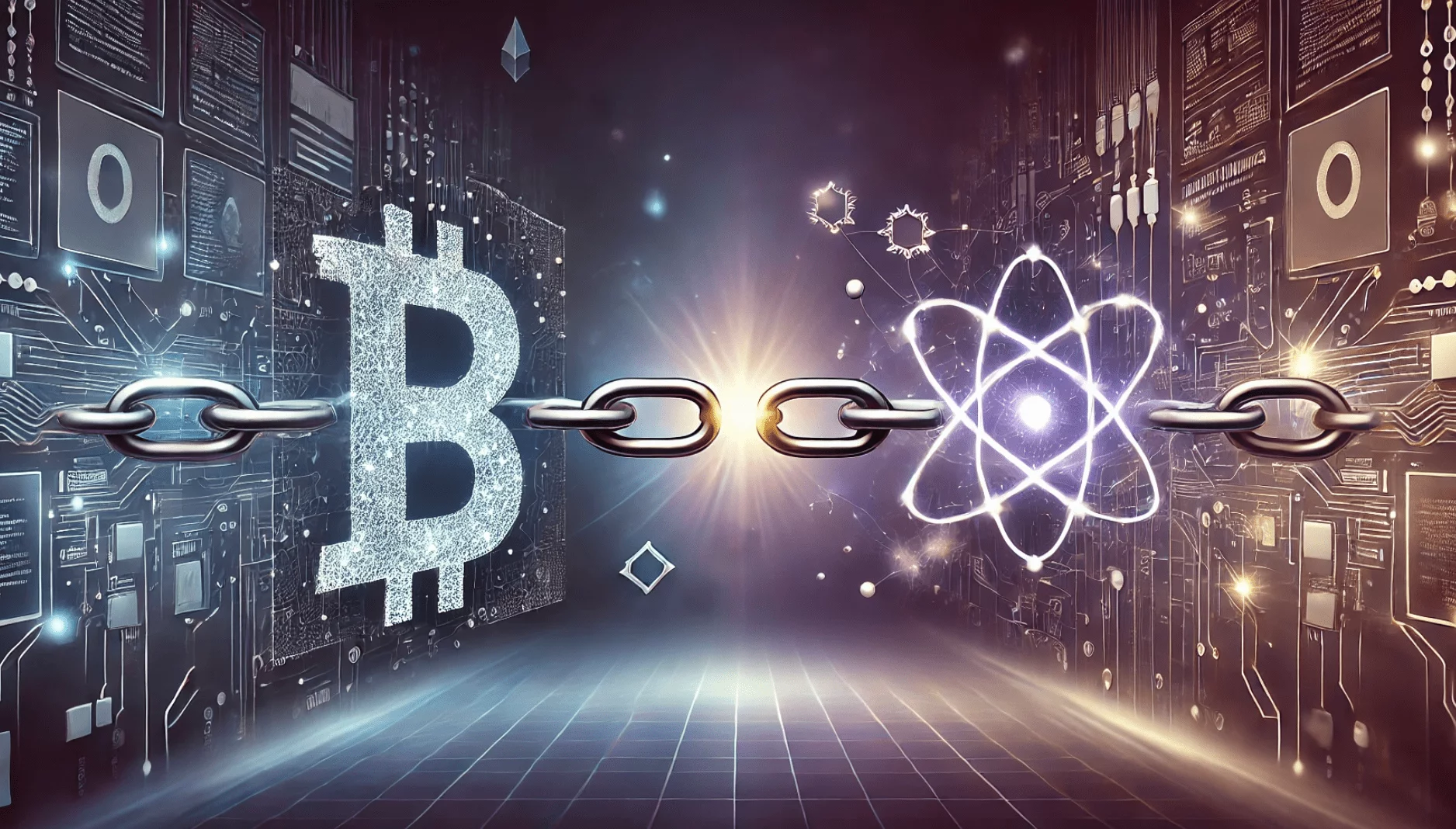
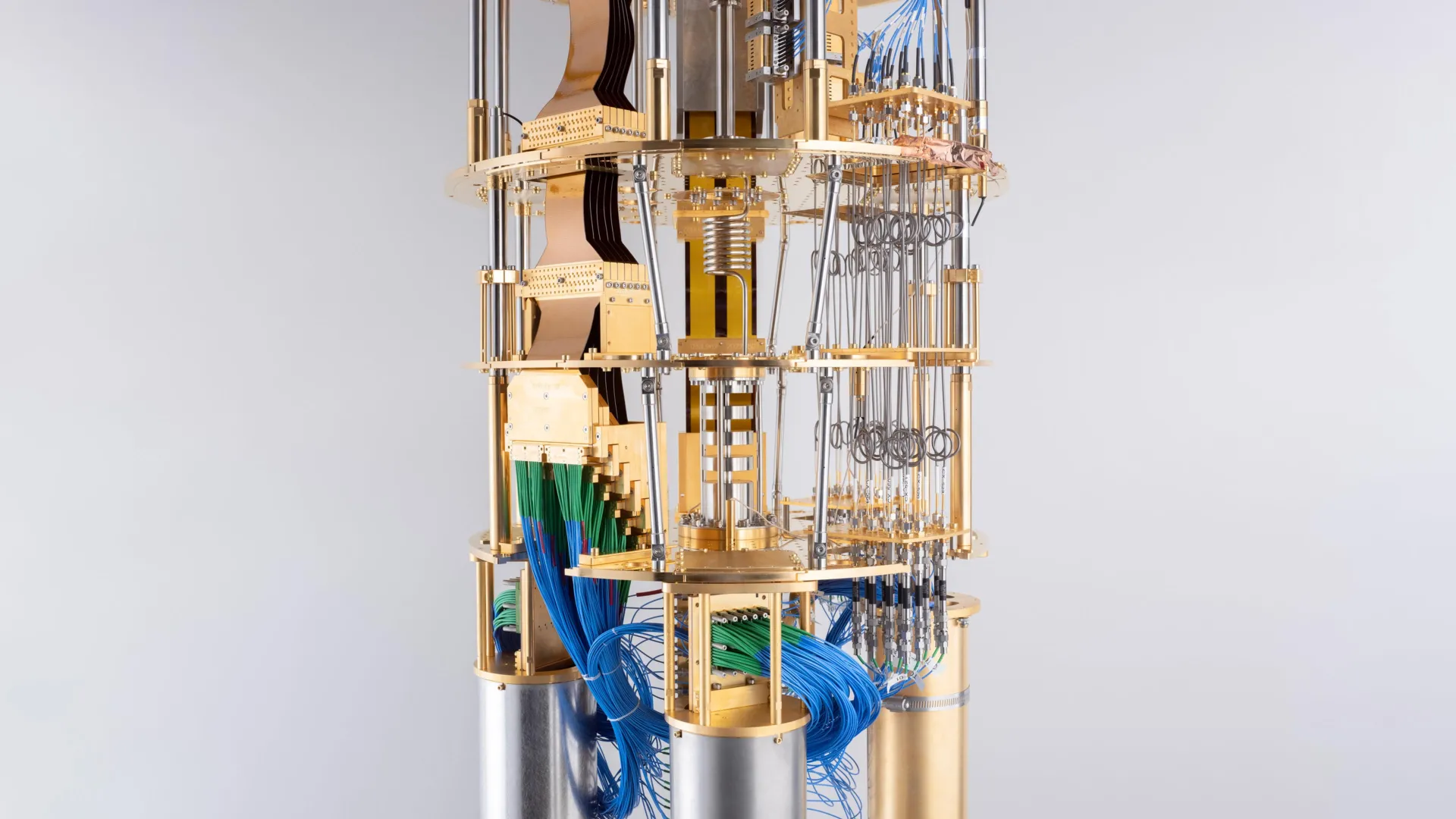
IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
Jun 10, 2025
IonQ Acquires Oxford Ionics for $1.08 Billion: A Bold Leap Toward Fault‑Tolerant Quantum Computing
Jun 9, 2025



Post‑Quantum Cryptography Takes Center Stage at Infosecurity Europe 2025
Jun 7, 2025



Oxford Quantum Circuits Unveils Bold Roadmap to 50,000 Logical Qubits by 2034
Jun 5, 2025



Caltech Achieves Hyper-Entanglement: A Quantum Breakthrough with Major Implications
Jun 5, 2025



Massive Data Breach Exposes Apple ID Logins: Why Post-Quantum Cryptography Must Start Now
Jun 4, 2025



A Quantum Celebration: UN Declares 2025 the International Year of Quantum Science and Technology
Jun 4, 2025



Crypto Asset Manager Grayscale Eyes the Quantum Frontier with Proposed Quantum Computing ETF
Jun 3, 2025
Quantum Entanglement: The Spooky Phenomenon That Could Transform Technology
Jun 2, 2025



Colt, Honeywell, and Nokia Launch Space-Based Trial for Quantum-Safe Cryptography
Jun 2, 2025



Surrogate Models Take Center Stage: A Smarter Way to Optimize Quantum Networks
May 31, 2025



Securing the Internet of Things: Why Post-Quantum Cryptography Is Critical for IoT's Future
May 30, 2025
Nord Quantique’s Multimode Qubit Breakthrough: A Leap Toward Scalable Quantum Computing
May 30, 2025
The 2025 Retail Cyberstorm: How Post-Quantum Cryptography Could Have Prevented Major Breaches
May 29, 2025



Microsoft’s Quantum Leap: Inside the Majorana Chip That Could Revolutionize Computing
May 29, 2025



Should Post-Quantum Cryptography Start Now? The Clock Is Ticking
May 28, 2025



Cracking RSA with Fewer Qubits: What Google's New Quantum Factoring Estimate Means for Cybersecurity
May 28, 2025



Quantum Arms Race: U.S. Defense Intelligence Flags Rivals’ Growing Military Use of Quantum Tech
May 27, 2025



Quantum Threats and Bitcoin: Why BlackRock’s Warning Matters for the Future of Crypto Security
May 27, 2025



Sudbury's SNOLAB Ventures into Quantum Computing Research
May 26, 2025
Lockheed Martin and IBM Pioneer Quantum-Classical Hybrid Computing for Complex Molecular Simulations
May 23, 2025



Why the Moon Matters for Quantum Computing: From Helium-3 to Off-Planet Quantum Networks
May 23, 2025



NIST Approves Three Post-Quantum Cryptography Standards: A Milestone for Digital Security
May 22, 2025



Scientists Connect Quantum Processors via Fiber Optic Cable for the First Time
May 21, 2025



Quantum Computing and Encryption Breakthroughs in 2025: A New Era of Innovation
May 21, 2025



How CISOs Can Defend Against the “Harvest Now, Decrypt Later” Threat
May 20, 2025



NVIDIA Expands Quantum and AI Ecosystem in Taiwan Through Strategic Partnerships and Supercomputing Initiatives
May 19, 2025



Quantum Annealing Breakthrough: Quantum Computer Outperforms Fastest Supercomputers
May 18, 2025



Quantum Computing's New Frontier: How the $1.4 Trillion US–UAE Investment Deal is Shaping the Industry
May 16, 2025



Quantum Computing Meets Cancer Research: A New Frontier in Drug Discovery
May 16, 2025



Quantum Industry Leaders Urge Congress to Reauthorize and Expand National Quantum Initiative
May 15, 2025



Honeywell's Quantinuum and Qatar's Al Rabban Capital Forge $1 Billion Quantum Computing Joint Venture
May 15, 2025



Advancing Quantum Machine Learning with Multi-Chip Ensemble Architectures
May 14, 2025



How will the new US-Saudi Arabia AI deal effect the Quantum Computing industry?
May 14, 2025



Saudi Arabia's $600 Billion AI Push: Amazon, Nvidia, and Global Tech Giants Lead the Charge
May 14, 2025



Quantum Computing Breakthrough: Diamond Qubits Achieve Unprecedented Precision
Apr 28, 2025



Australia’s Quantum Cryptography Roadmap: Preparing for a Post-Quantum Future
Apr 26, 2025



Harvest Now, Decrypt later
Apr 25, 2025



NIST’s New Quantum Cryptography Standards: What You Need to Know
Apr 25, 2025
Read our latest commentary and research on the post-quantum encryption space
Read our latest commentary and research on the post-quantum encryption space
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack


Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire


Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report


Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse


Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance


Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
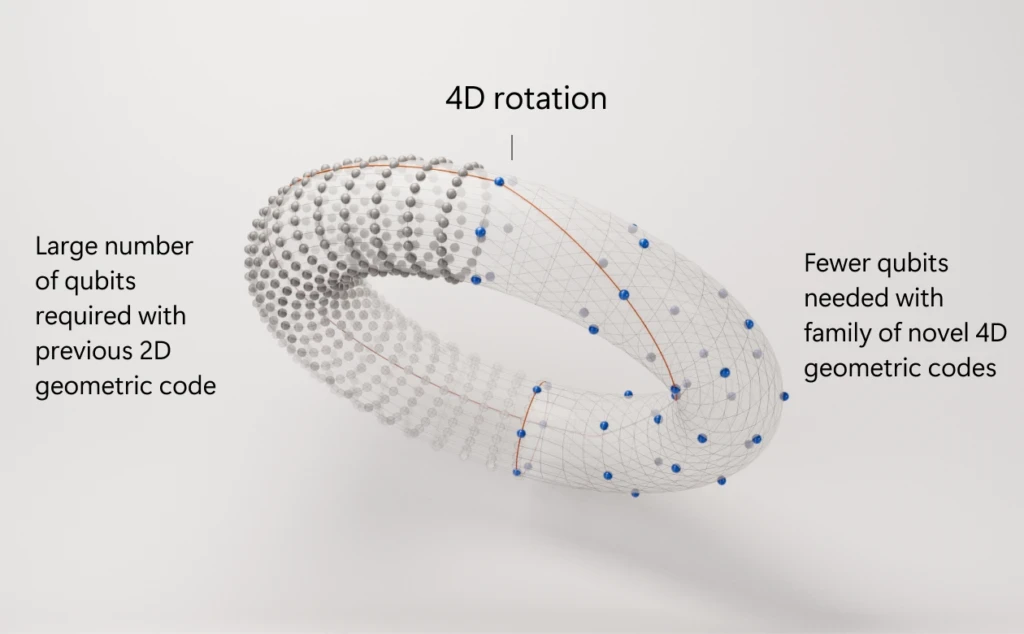
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors


How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack


IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer


Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence


Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025


Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing


Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’


IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack

Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire

Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report

Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse

Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance

Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
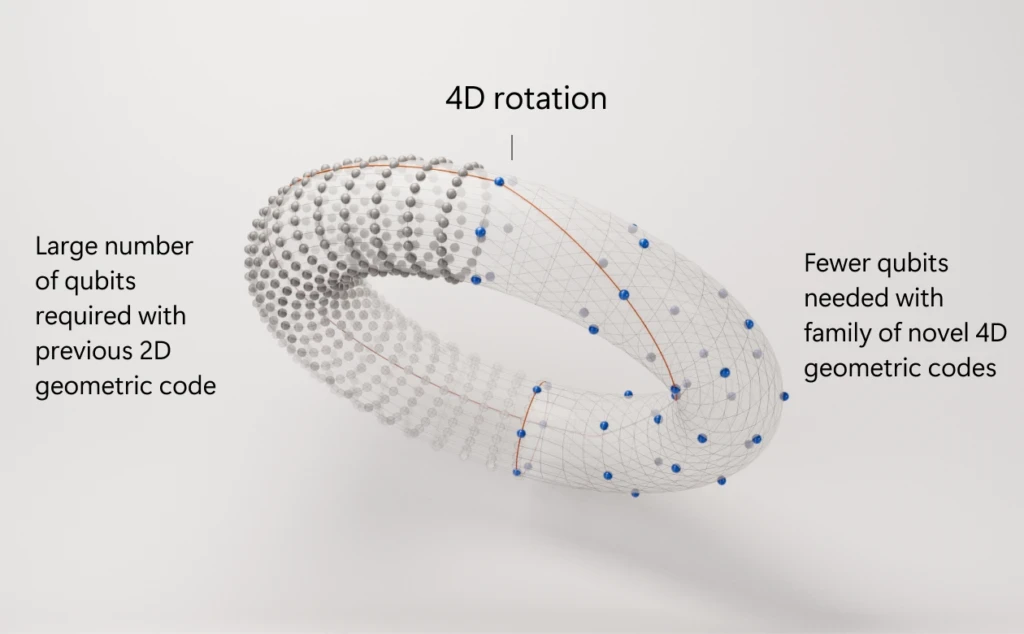
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors

How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack

IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer

Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence

Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025

Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing

Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’

IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
"Harvest Now, Decrypt Later": The Quiet Threat to Data Security
In the ever-evolving world of cybersecurity, one looming threat has experts particularly concerned: "Harvest Now, Decrypt Later" (HNDL) attacks. While the name might sound like a sci-fi subplot, the concept is simple and the danger is very real—especially as quantum computing moves from theory to reality.
What Is "Harvest Now, Decrypt Later"?
A "Harvest Now, Decrypt Later" strategy refers to a long-term cyberattack where a malicious actor intercepts and stores encrypted data today with the intent of decrypting it in the future when more powerful computing—especially quantum computers—can break current encryption standards.
In simpler terms, it’s like stealing a locked safe today, knowing you don’t have the key but betting that one day you'll have the lock-picking tools needed to open it.
Why Is This a Big Deal?
Most of the world’s sensitive data—banking information, medical records, government communications, intellectual property—is protected by encryption standards like RSA, ECC, and AES. These encryption systems are strong against traditional computers but could be broken relatively easily by future quantum computers using algorithms like Shor’s algorithm or Grover’s algorithm.
This creates a dangerous mismatch: data that is encrypted securely today could become fully exposed tomorrow. And by "tomorrow," we mean a future that could be just 5 to 15 years away, depending on the pace of quantum advancements.
What Kind of Data Is at Risk?
Not all data has the same shelf life. Some data becomes irrelevant within hours, while other information remains sensitive for decades. Here are some prime targets for HNDL attacks:
Military and diplomatic communications
Healthcare and genetic data
Corporate trade secrets
Research and development blueprints
Financial records
User credentials
In short: anything that could still be valuable or damaging in the future is fair game.
Who’s Doing This?
While specific actors are hard to identify, experts believe that nation-states with the resources to develop quantum technologies (such as the U.S., China, and Russia) are the most likely candidates to be engaging in "Harvest Now, Decrypt Later" operations.
These attacks are attractive because they can be carried out covertly. A spy agency doesn’t need to break into a network; they just need to passively tap into communication lines, download encrypted traffic, and store it for the long haul.
What Can Be Done About It?
This threat is already being taken seriously. The cybersecurity community is actively working on a new generation of cryptographic algorithms known as Post-Quantum Cryptography (PQC)—encryption methods that are designed to withstand the immense power of quantum computing.
Organizations like the National Institute of Standards and Technology (NIST) have been leading efforts to standardize post-quantum cryptographic algorithms. In 2022, NIST announced its initial selections for quantum-resistant encryption, which are now being prepared for widespread adoption.
Steps You Can Take Now
While we wait for quantum computers to mature, there are several proactive steps that individuals and organizations can take:
Audit your data: Identify which data has long-term confidentiality requirements.
Adopt crypto agility: Design systems that can easily switch to new encryption algorithms.
Start experimenting with post-quantum solutions: Pilot PQC options and stay informed on NIST’s progress.
Monitor for suspicious activity: Just because someone can’t decrypt traffic today doesn’t mean they aren’t harvesting it.
Educate your team: Make sure your cybersecurity professionals are aware of quantum threats and future-proofing strategies.
Final Thoughts
“Harvest Now, Decrypt Later” is a quiet, patient form of cyber-espionage that bets on the future. And with quantum computing advancing rapidly, that future might be closer than we think. If organizations don’t begin to prepare now, they may find themselves caught off-guard when yesterday’s stolen secrets become tomorrow’s biggest security breach.
Quantum-safe security isn’t just a buzzword—it’s becoming a necessity.
Let's talk!
Office:
1535 Broadway
New York, NY 10036
USA
Local time:
11:49:51
Let's talk!
Office:
1535 Broadway
New York, NY 10036
USA
Local time:
11:49:51
