Cracking RSA with Fewer Qubits: What Google's New Quantum Factoring Estimate Means for Cybersecurity
Cracking RSA with Fewer Qubits: What Google's New Quantum Factoring Estimate Means for Cybersecurity
May 28, 2025
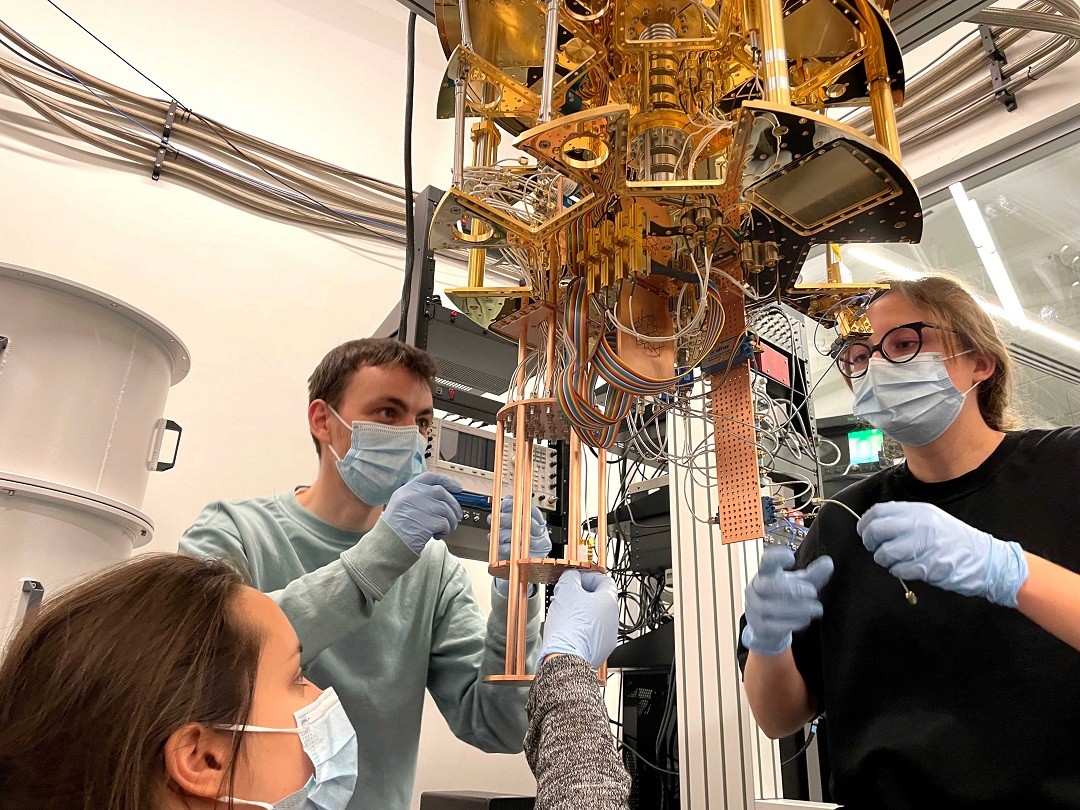
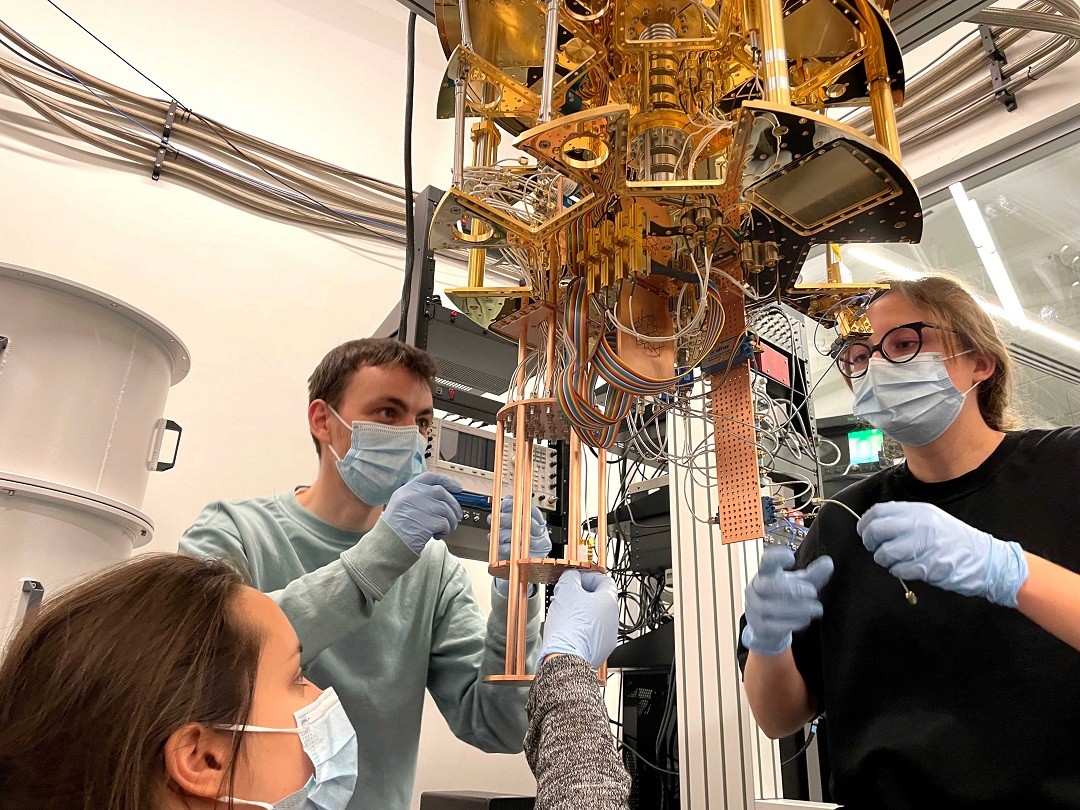
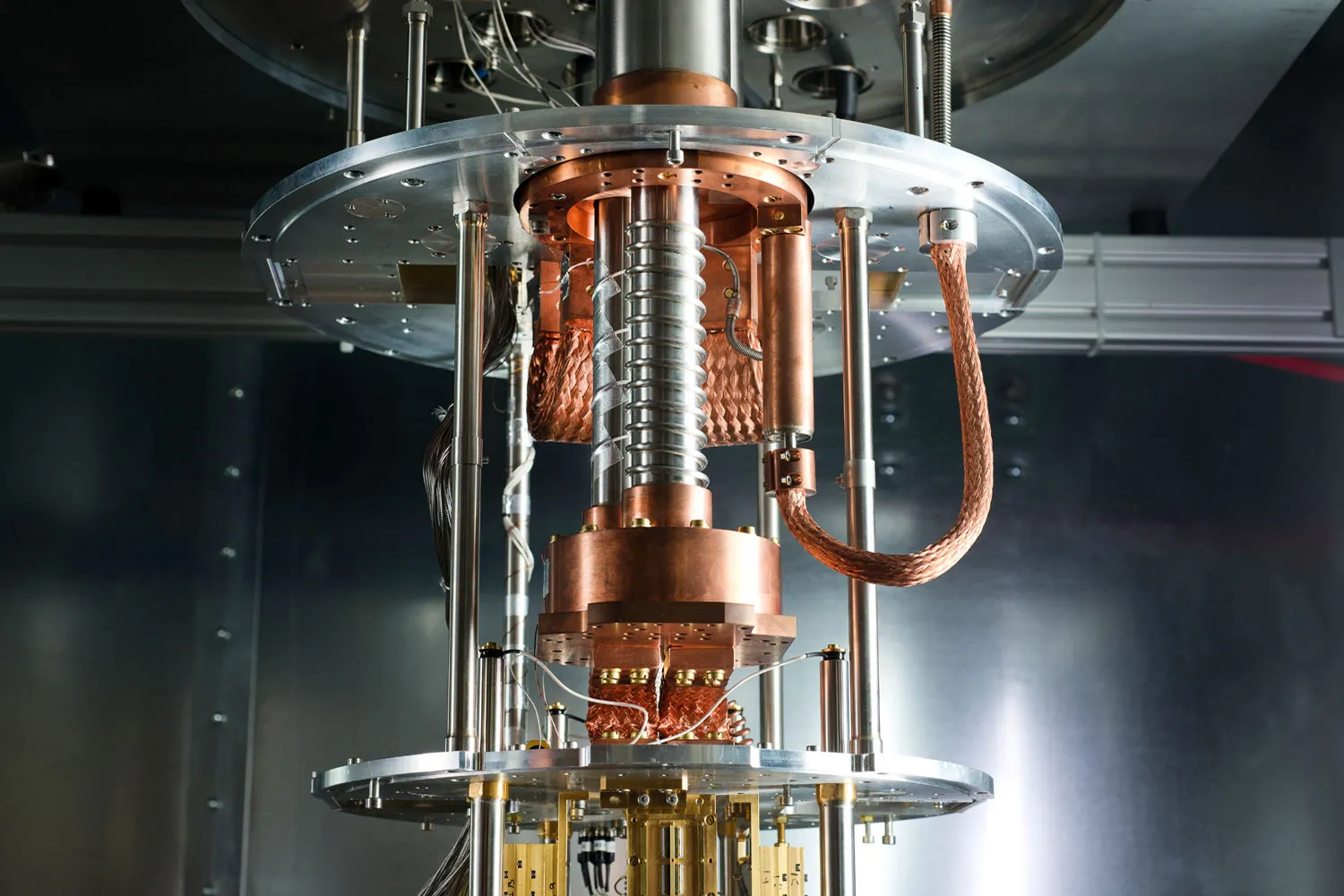
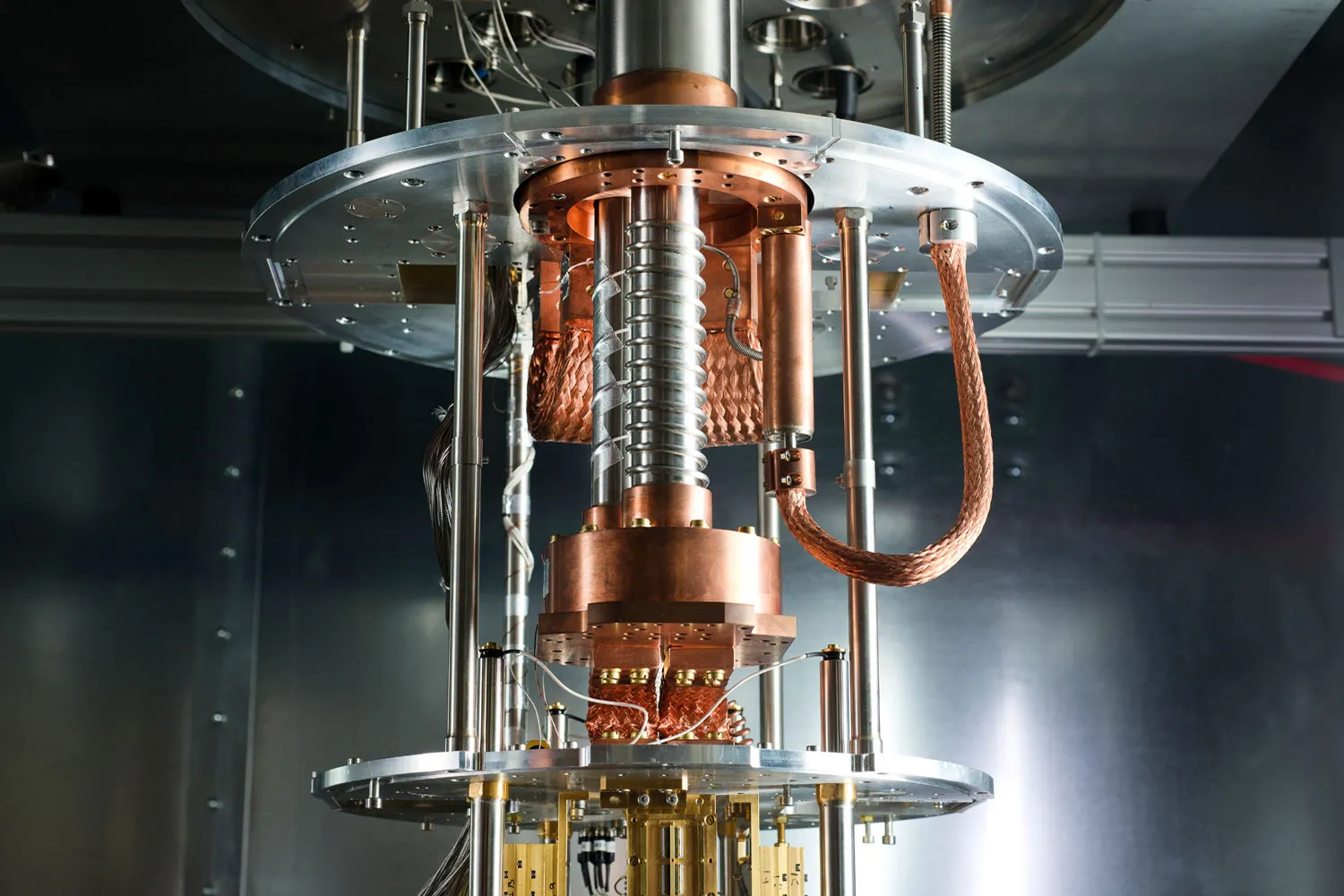
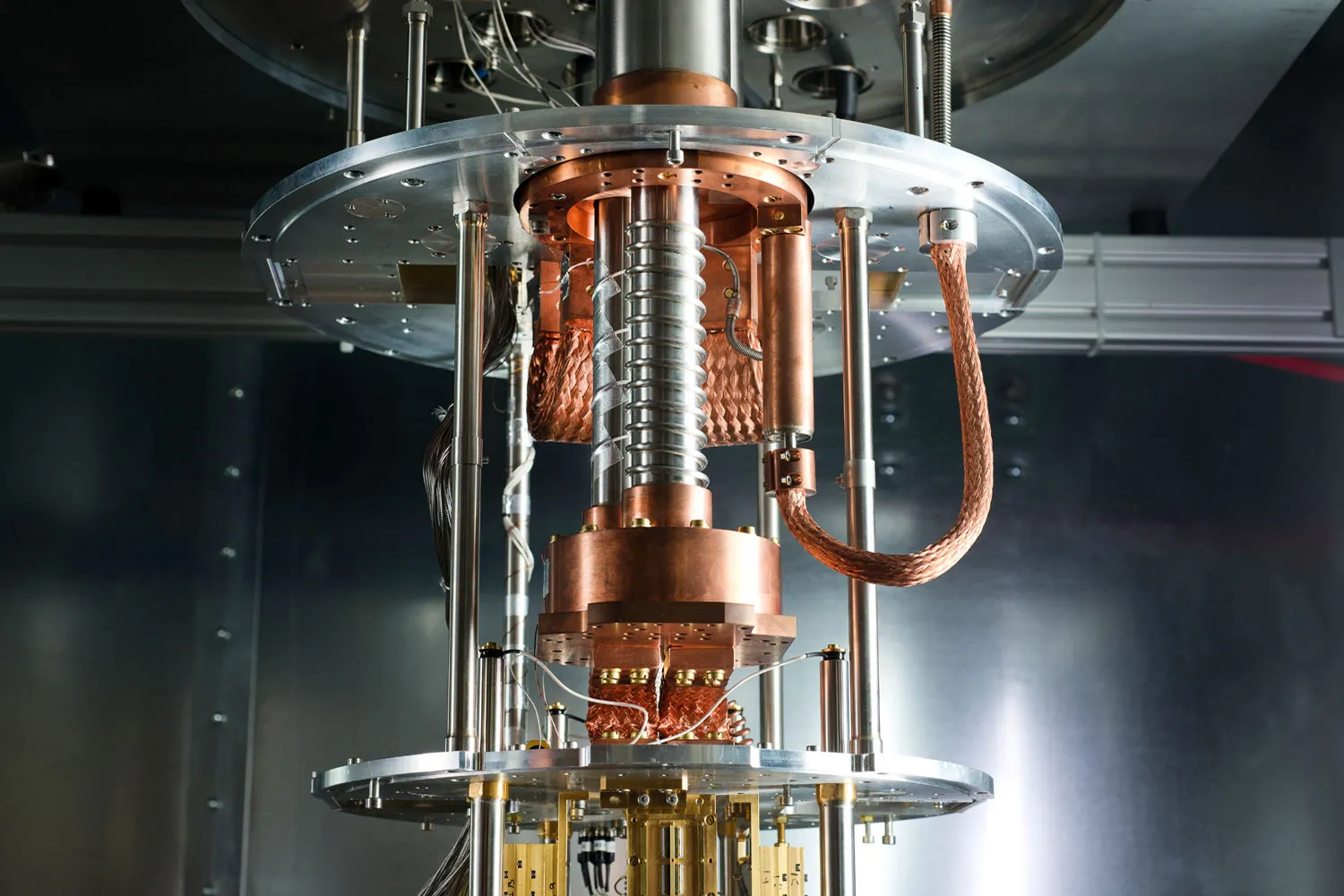
Last week, Craig Gidney from Google Quantum AI published a breakthrough study that redefines the landscape of cryptographic security. His paper, “How to factor 2048 bit RSA integers with less than a million noisy qubits”, dramatically lowers the estimated quantum resources needed to break RSA-2048—one of the most widely used encryption standards securing everything from email to financial transactions to government databases.
Where previous estimates (including Gidney’s own 2019 study) projected that cracking RSA-2048 would require around 20 million qubits and 8 hours of computation, the new analysis reveals that it could be done in under a week using fewer than 1 million noisy qubits. This reduction of more than 95% in hardware requirements is a seismic shift in the projected timeline for “Q-Day”—the hypothetical moment when quantum computers can break modern encryption.
Read QuantumGenie's other industry insights.
What Makes RSA-2048 Vulnerable?
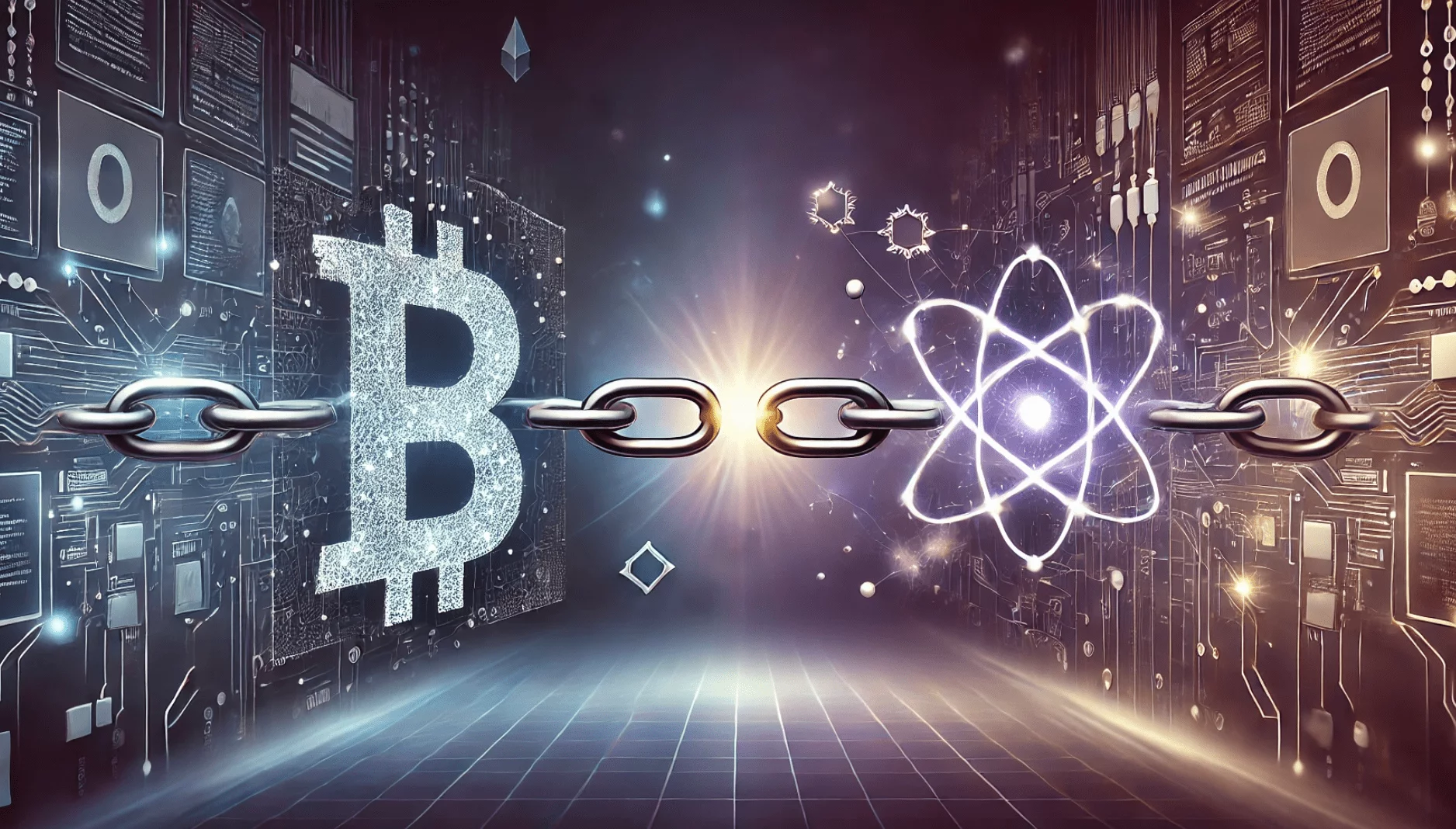
RSA encryption is based on the mathematical challenge of factoring large numbers into their prime components—a task that classical computers find prohibitively difficult at the 2048-bit level. This difficulty forms the backbone of digital security protocols used in secure web browsing (HTTPS), email encryption (PGP), VPNs, and many blockchain systems.
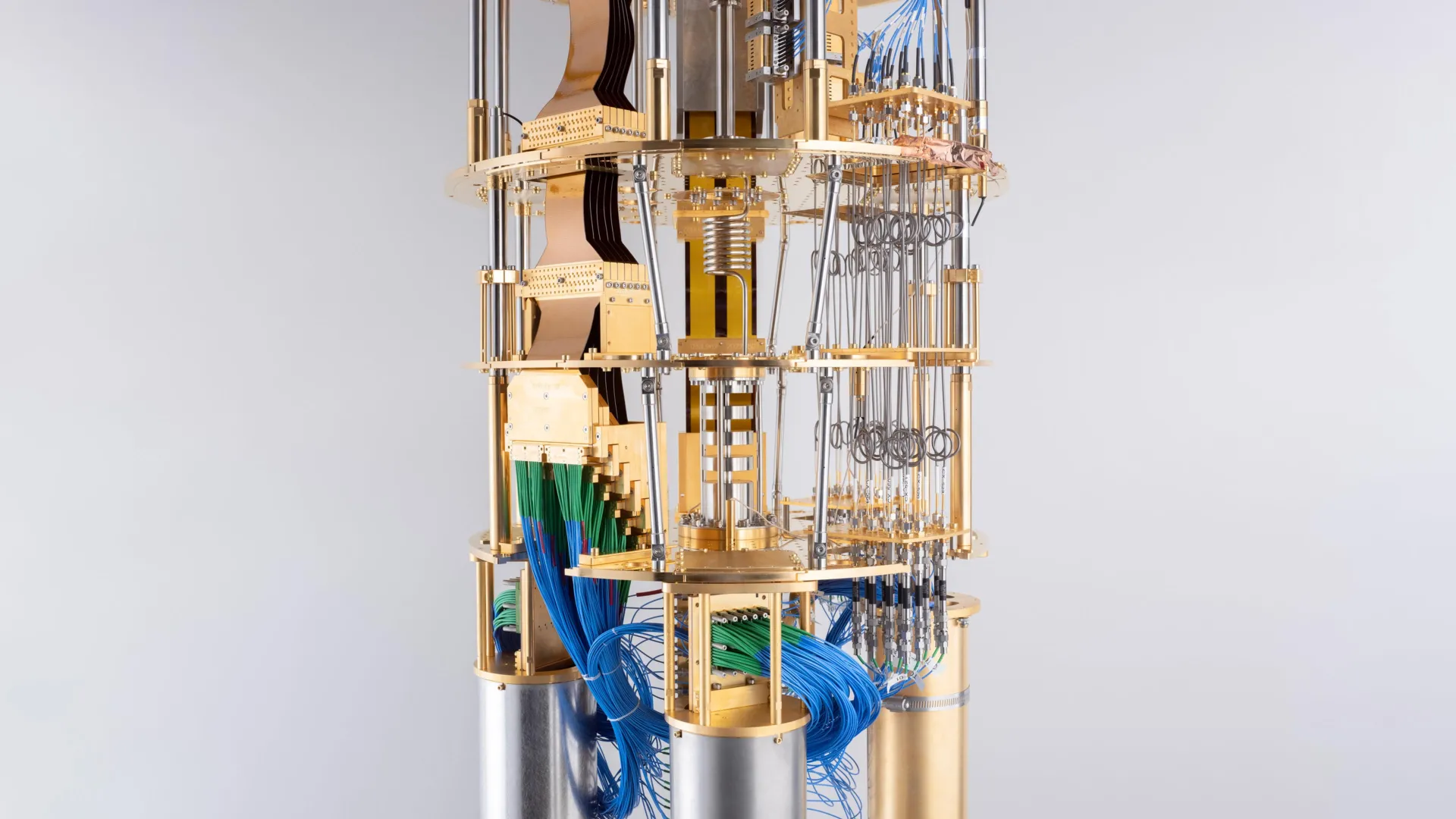
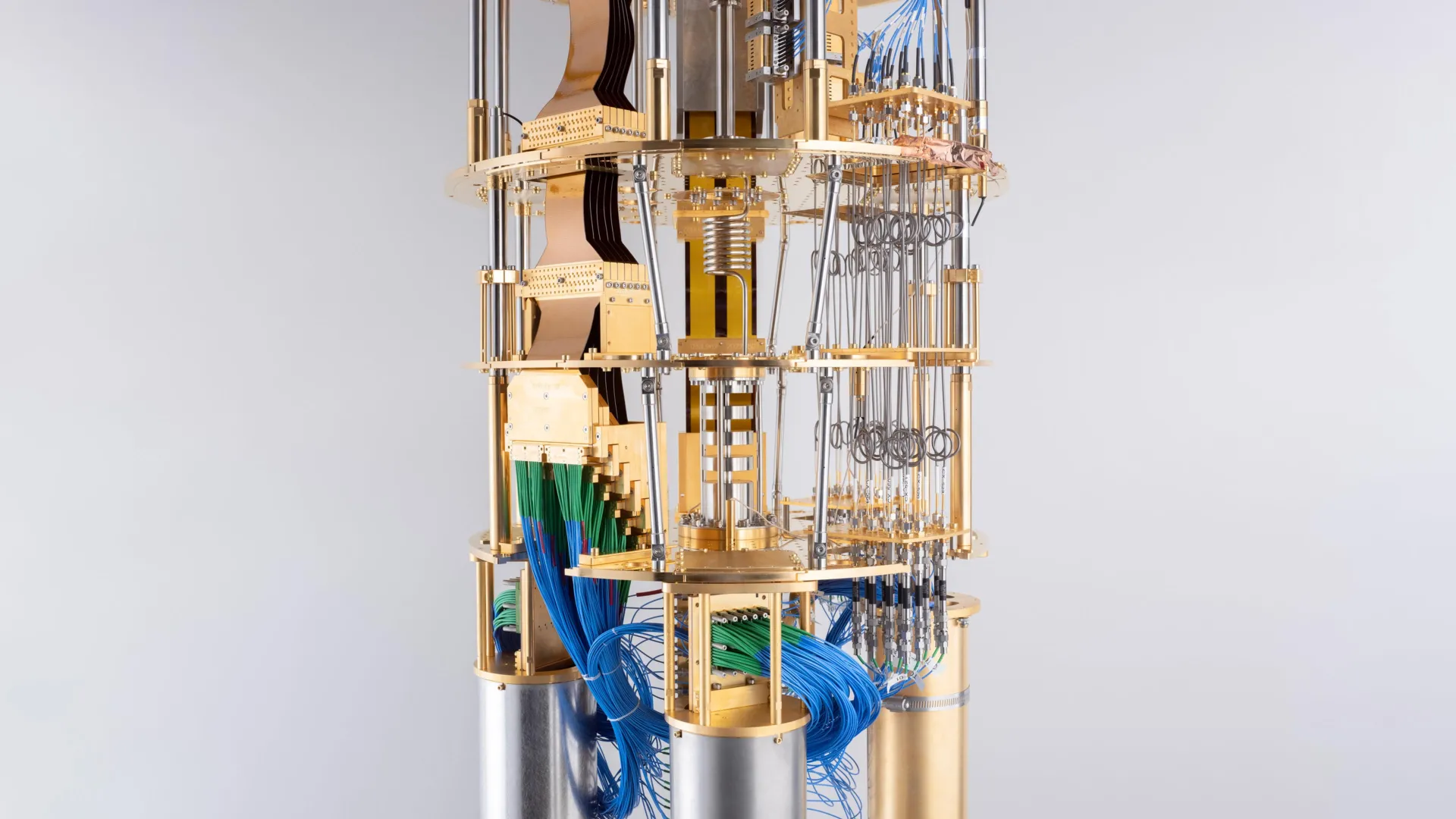
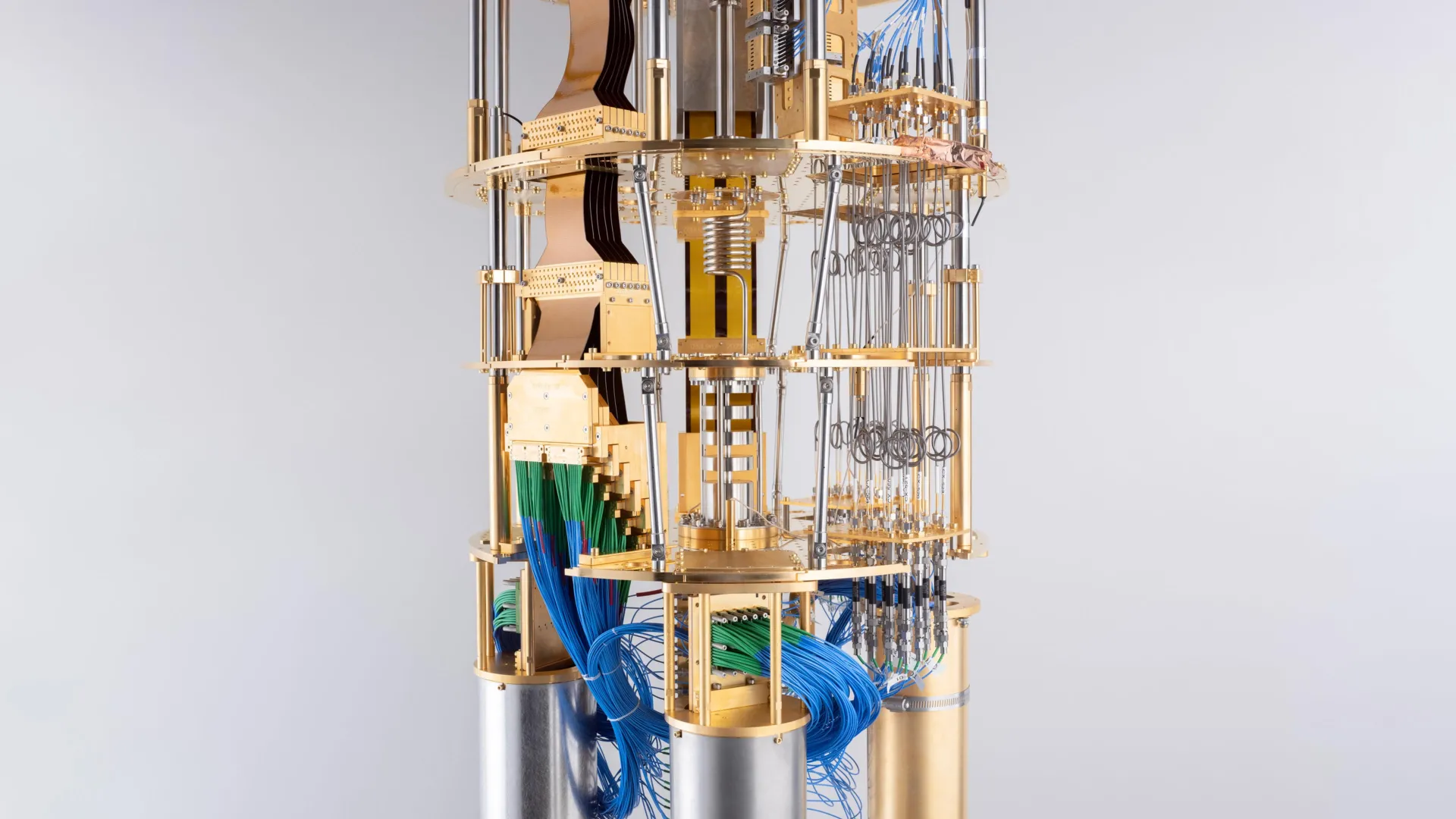
Quantum computers, however, can use Shor’s algorithm to factor these numbers exponentially faster. The catch? That algorithm requires high-fidelity quantum gates, large-scale error correction, and millions of qubits—until now.
Google’s Innovation: Shrinking the Qubit Budget
Gidney’s 2025 paper showcases several technical innovations that slash the qubit requirements for factoring RSA-2048:
Approximate Residue Arithmetic: This method, recently introduced by Chevignard, Fouque, and Schrottenloher (2024), streamlines modular arithmetic and reduces the depth of quantum circuits needed for number factoring.
Magic State Cultivation: A more space-efficient way of producing non-Clifford gate resources (known as magic states), crucial for enabling universal quantum computation under error correction.
Optimized Period Finding with Ekerå-Håstad Algorithms: These advanced number-theoretic optimizations allow for a more efficient implementation of the quantum part of Shor’s algorithm.
Yoked Surface Codes & Sparse Lookups: Techniques that minimize the overhead in fault-tolerant quantum circuits, enabling better scaling.
Collectively, these improvements reduce the physical qubit requirement to under 1 million and allow the algorithm to complete in less than 7 days, given favorable assumptions like a 0.1% gate error rate and a 1-microsecond surface code cycle time.
This represents a ~20x reduction in required qubits and vastly improves the practical feasibility of quantum attacks on RSA.
Read QuantumGenie's other industry insights.
Implications for Cryptographic Security
The broader takeaway is stark: RSA-2048 is no longer as safe as once believed.
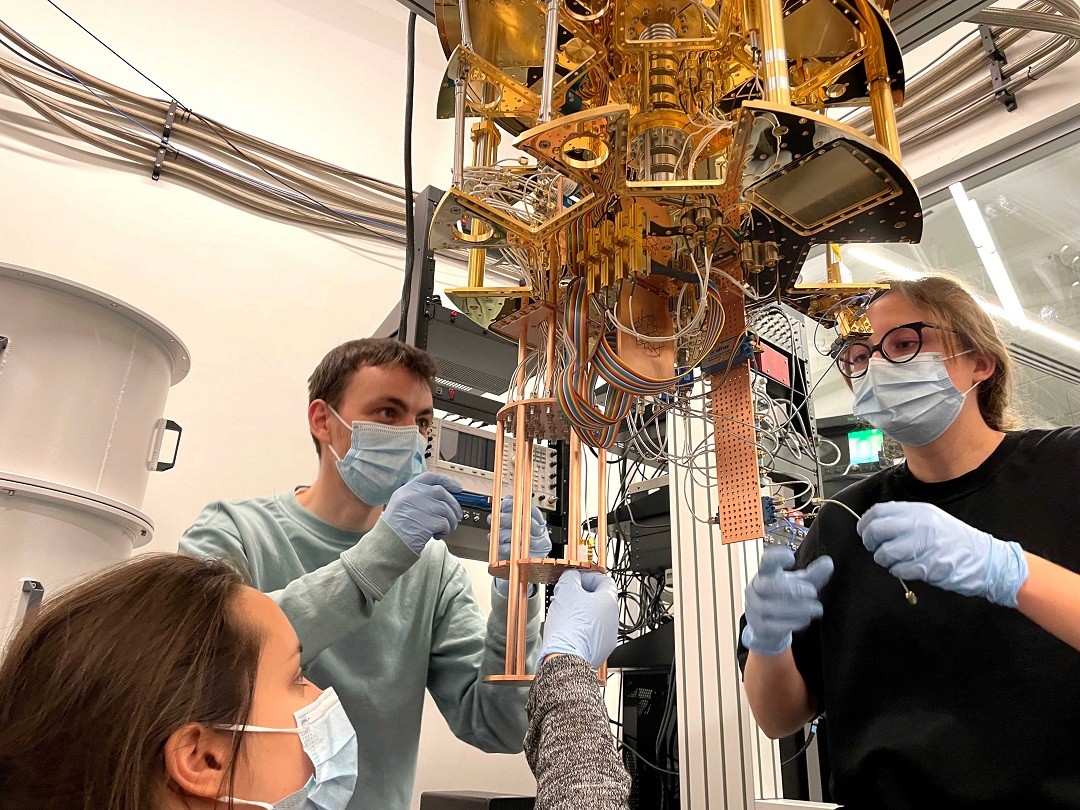
While building a quantum computer capable of executing this attack is still a monumental engineering challenge, the new resource estimates bring that future much closer. If quantum hardware continues to progress as expected—with leading players like IBM, Google, and startups like Quantinuum and PsiQuantum scaling up both qubit numbers and error rates—Q-Day could realistically occur within 10 to 15 years, or sooner in a best-case scenario.
That means data encrypted today could be vulnerable tomorrow—especially for governments, banks, healthcare institutions, and cloud service providers that store data with long-term confidentiality requirements.
This underscores the risk of “harvest now, decrypt later” attacks, in which threat actors (including nation-states) are believed to be storing encrypted traffic now, anticipating that they’ll be able to decrypt it once quantum systems mature.
Read QuantumGenie's other industry insights.
Urgency for Post-Quantum Cryptography (PQC)
The cryptographic community has been preparing for this scenario for several years. The National Institute of Standards and Technology (NIST) has already finalized the first suite of post-quantum encryption standards, including lattice-based algorithms like CRYSTALS-Kyber and Dilithium, which are believed to be resistant to quantum attacks.
Yet, many systems—particularly in legacy environments—still depend on RSA-2048 or similar classical algorithms. Migrating these systems takes time, and in some cases, the encrypted data will need to remain secure for decades. That’s why Gidney’s paper acts as both a technical milestone and a public warning.
Organizations must start:
Inventorying existing cryptographic systems and identifying where RSA is used.
Deploying hybrid encryption (combining classical and quantum-resistant algorithms).
Adopting crypto-agility strategies to enable rapid algorithm updates in the future.
Educating stakeholders and regulators about the urgency of quantum readiness.
Read QuantumGenie's other industry insights.
Conclusion: The Countdown Is Real
Google’s 2025 quantum factoring estimate is more than a mathematical triumph—it’s a wake-up call. RSA-2048 has long been considered a gold standard in security, but this research makes clear that its lifespan is rapidly approaching an end.
The clock is ticking. And for the cybersecurity world, there’s no time to waste.
Reference:
Gidney, C. (2025). How to factor 2048 bit RSA integers with less than a million noisy qubits. Google Quantum AI. arXiv:2505.15917.
Need help evaluating your organization’s quantum risk exposure or building a migration roadmap? I can help design a tailored post-quantum strategy.
May 28, 2025
Quantum Insights
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack
Jul 21, 2025



Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire
Jul 20, 2025



Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Jul 17, 2025
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report
Jul 14, 2025



Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse
Jul 10, 2025



Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance
Jul 8, 2025



Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
Jun 26, 2025
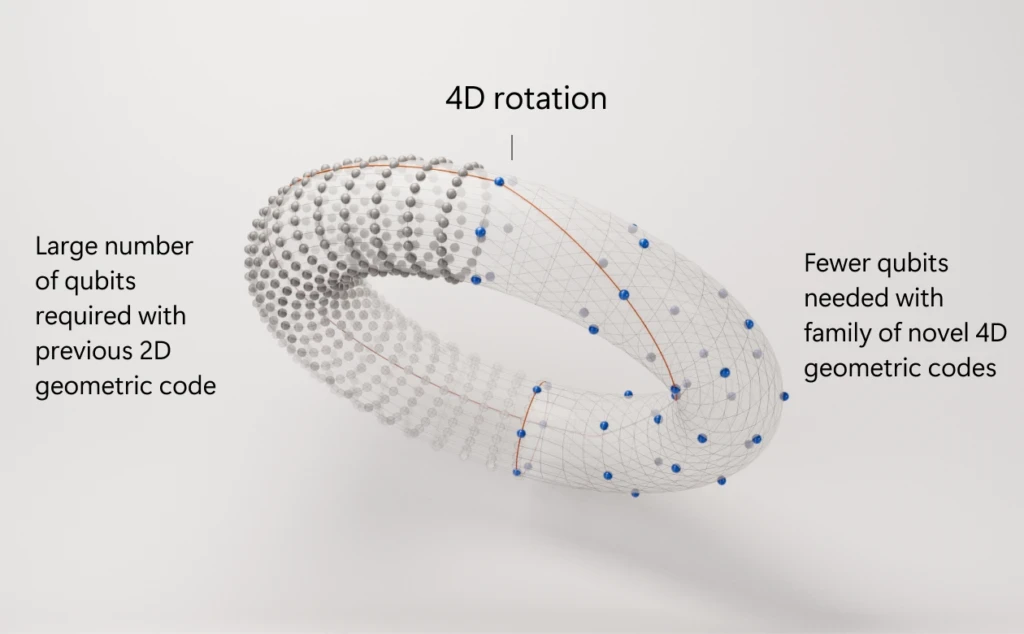
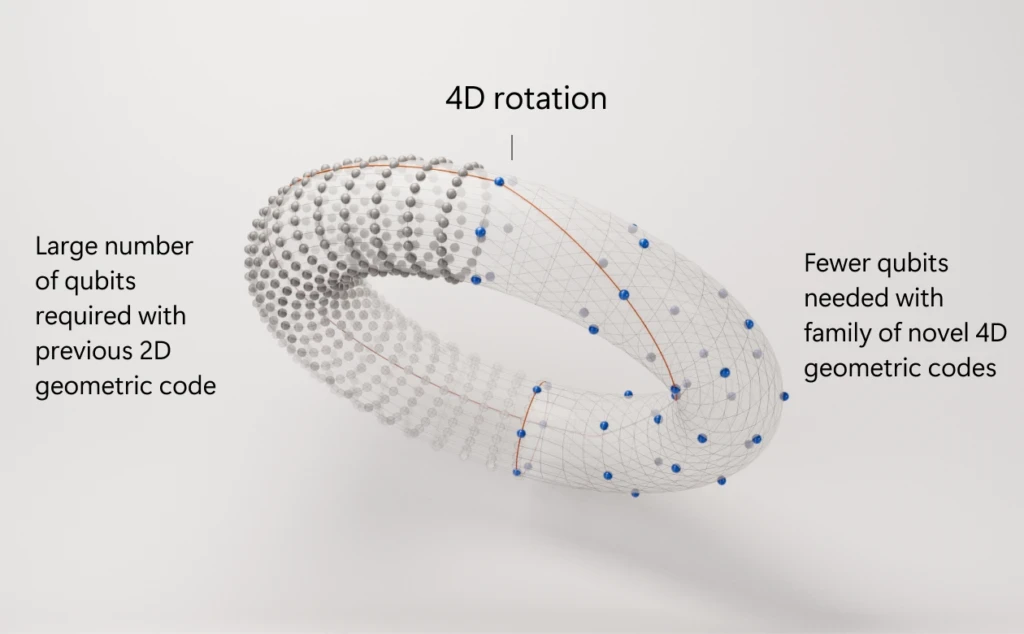
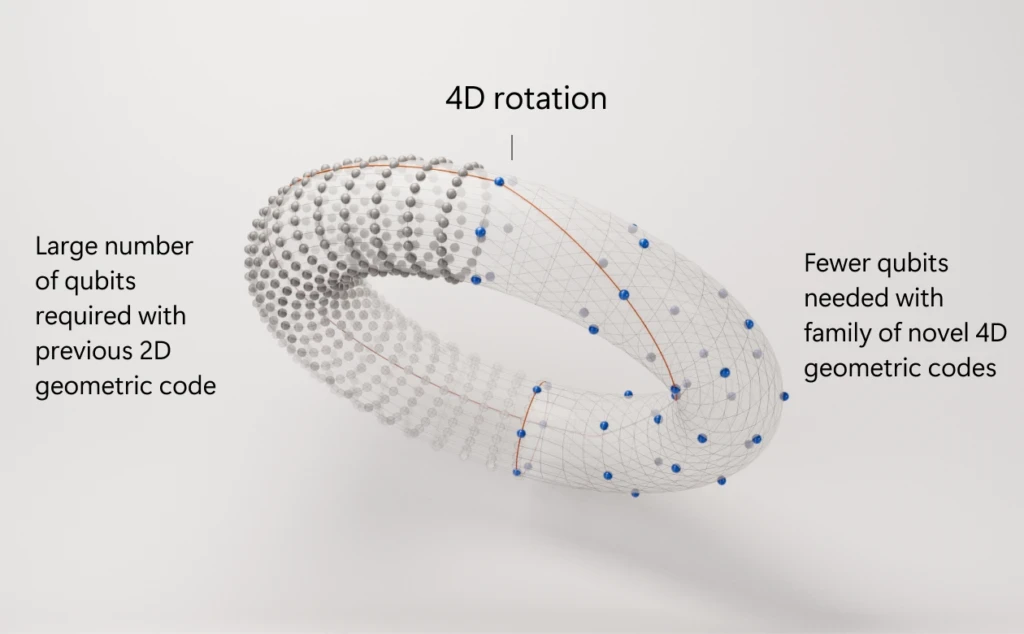
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors
Jun 22, 2025



How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack



IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer
Jun 18, 2025



Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence
Jun 17, 2025



Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025
Jun 15, 2025



Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing
Jun 12, 2025



Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’
Jun 11, 2024



IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
Jun 10, 2025
IonQ Acquires Oxford Ionics for $1.08 Billion: A Bold Leap Toward Fault‑Tolerant Quantum Computing
Jun 9, 2025



Post‑Quantum Cryptography Takes Center Stage at Infosecurity Europe 2025
Jun 7, 2025



Oxford Quantum Circuits Unveils Bold Roadmap to 50,000 Logical Qubits by 2034
Jun 5, 2025



Caltech Achieves Hyper-Entanglement: A Quantum Breakthrough with Major Implications
Jun 5, 2025



Massive Data Breach Exposes Apple ID Logins: Why Post-Quantum Cryptography Must Start Now
Jun 4, 2025



A Quantum Celebration: UN Declares 2025 the International Year of Quantum Science and Technology
Jun 4, 2025



Crypto Asset Manager Grayscale Eyes the Quantum Frontier with Proposed Quantum Computing ETF
Jun 3, 2025
Quantum Entanglement: The Spooky Phenomenon That Could Transform Technology
Jun 2, 2025



Colt, Honeywell, and Nokia Launch Space-Based Trial for Quantum-Safe Cryptography
Jun 2, 2025



Surrogate Models Take Center Stage: A Smarter Way to Optimize Quantum Networks
May 31, 2025



Securing the Internet of Things: Why Post-Quantum Cryptography Is Critical for IoT's Future
May 30, 2025
Nord Quantique’s Multimode Qubit Breakthrough: A Leap Toward Scalable Quantum Computing
May 30, 2025
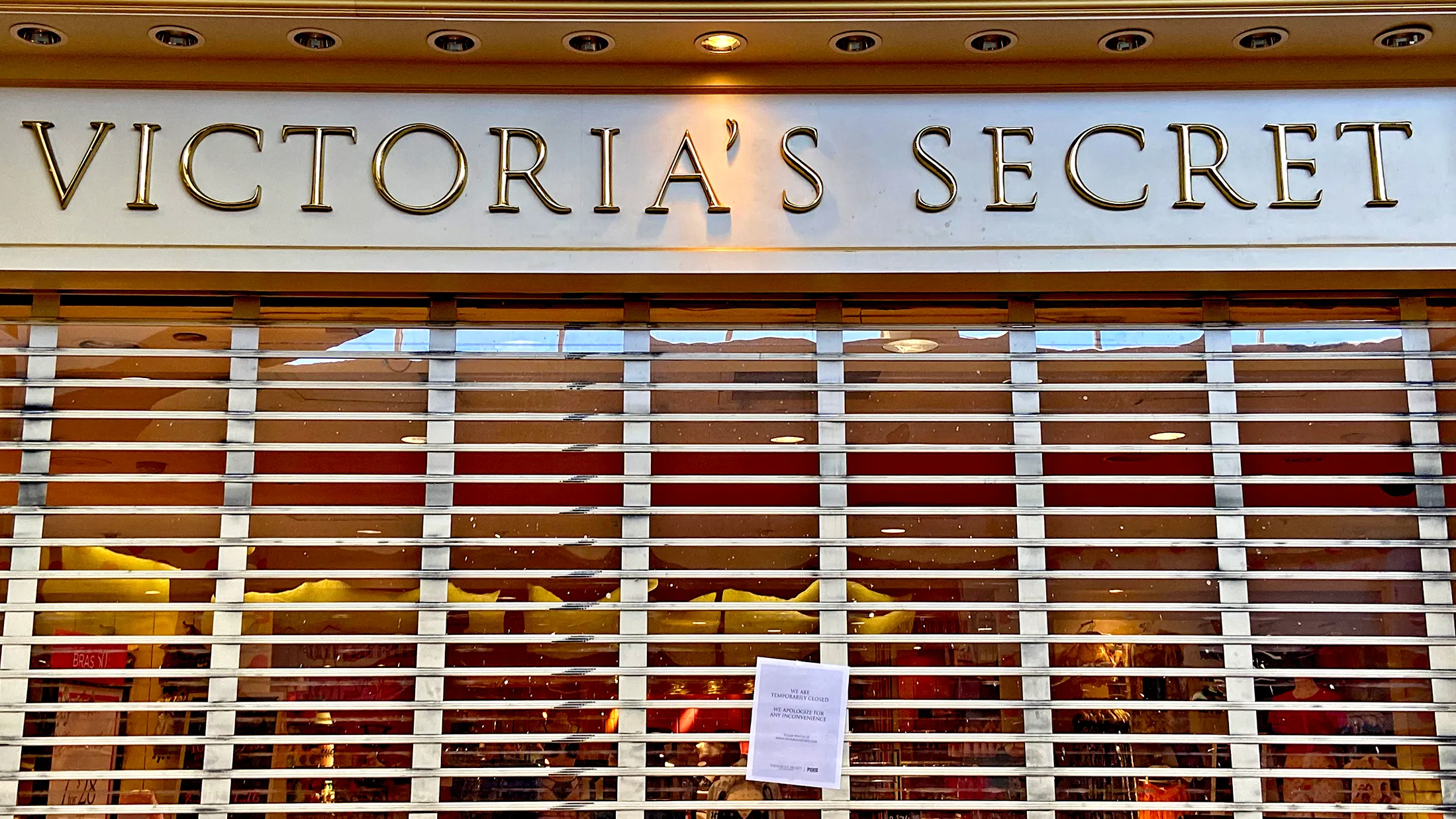
The 2025 Retail Cyberstorm: How Post-Quantum Cryptography Could Have Prevented Major Breaches
May 29, 2025



Microsoft’s Quantum Leap: Inside the Majorana Chip That Could Revolutionize Computing
May 29, 2025



Should Post-Quantum Cryptography Start Now? The Clock Is Ticking
May 28, 2025



Cracking RSA with Fewer Qubits: What Google's New Quantum Factoring Estimate Means for Cybersecurity
May 28, 2025



Quantum Arms Race: U.S. Defense Intelligence Flags Rivals’ Growing Military Use of Quantum Tech
May 27, 2025



Quantum Threats and Bitcoin: Why BlackRock’s Warning Matters for the Future of Crypto Security
May 27, 2025



Sudbury's SNOLAB Ventures into Quantum Computing Research
May 26, 2025
Lockheed Martin and IBM Pioneer Quantum-Classical Hybrid Computing for Complex Molecular Simulations
May 23, 2025



Why the Moon Matters for Quantum Computing: From Helium-3 to Off-Planet Quantum Networks
May 23, 2025



NIST Approves Three Post-Quantum Cryptography Standards: A Milestone for Digital Security
May 22, 2025



Scientists Connect Quantum Processors via Fiber Optic Cable for the First Time
May 21, 2025



Quantum Computing and Encryption Breakthroughs in 2025: A New Era of Innovation
May 21, 2025



How CISOs Can Defend Against the “Harvest Now, Decrypt Later” Threat
May 20, 2025



NVIDIA Expands Quantum and AI Ecosystem in Taiwan Through Strategic Partnerships and Supercomputing Initiatives
May 19, 2025



Quantum Annealing Breakthrough: Quantum Computer Outperforms Fastest Supercomputers
May 18, 2025



Quantum Computing's New Frontier: How the $1.4 Trillion US–UAE Investment Deal is Shaping the Industry
May 16, 2025



Quantum Computing Meets Cancer Research: A New Frontier in Drug Discovery
May 16, 2025



Quantum Industry Leaders Urge Congress to Reauthorize and Expand National Quantum Initiative
May 15, 2025



Honeywell's Quantinuum and Qatar's Al Rabban Capital Forge $1 Billion Quantum Computing Joint Venture
May 15, 2025



Advancing Quantum Machine Learning with Multi-Chip Ensemble Architectures
May 14, 2025



How will the new US-Saudi Arabia AI deal effect the Quantum Computing industry?
May 14, 2025



Saudi Arabia's $600 Billion AI Push: Amazon, Nvidia, and Global Tech Giants Lead the Charge
May 14, 2025



Quantum Computing Breakthrough: Diamond Qubits Achieve Unprecedented Precision
Apr 28, 2025



Australia’s Quantum Cryptography Roadmap: Preparing for a Post-Quantum Future
Apr 26, 2025



Harvest Now, Decrypt later
Apr 25, 2025



NIST’s New Quantum Cryptography Standards: What You Need to Know
Apr 25, 2025
Read our latest commentary and research on the post-quantum encryption space
Read our latest commentary and research on the post-quantum encryption space
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack


Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire


Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report


Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse


Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance


Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
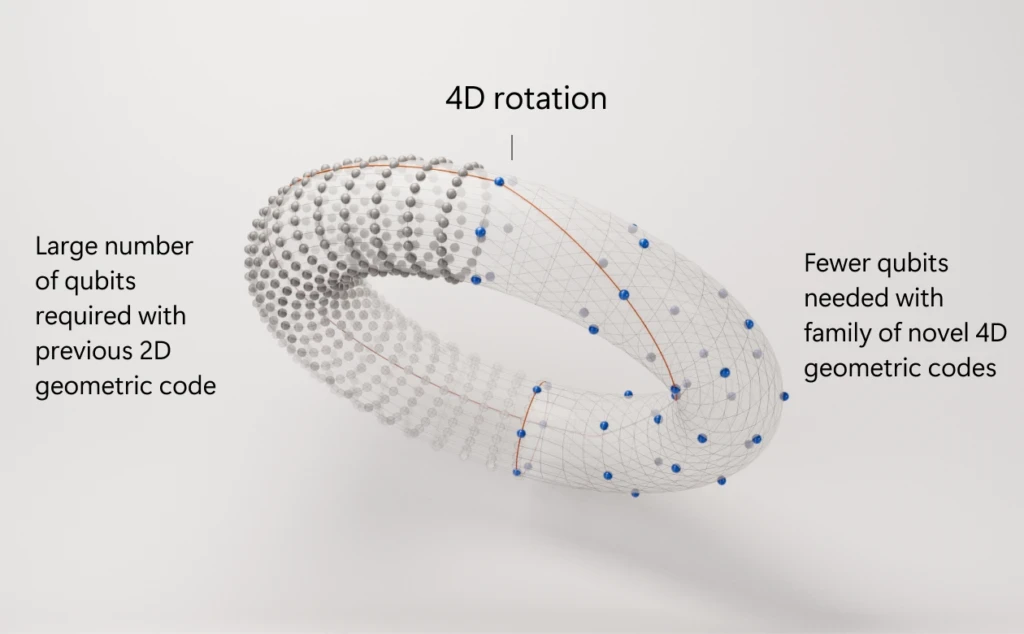
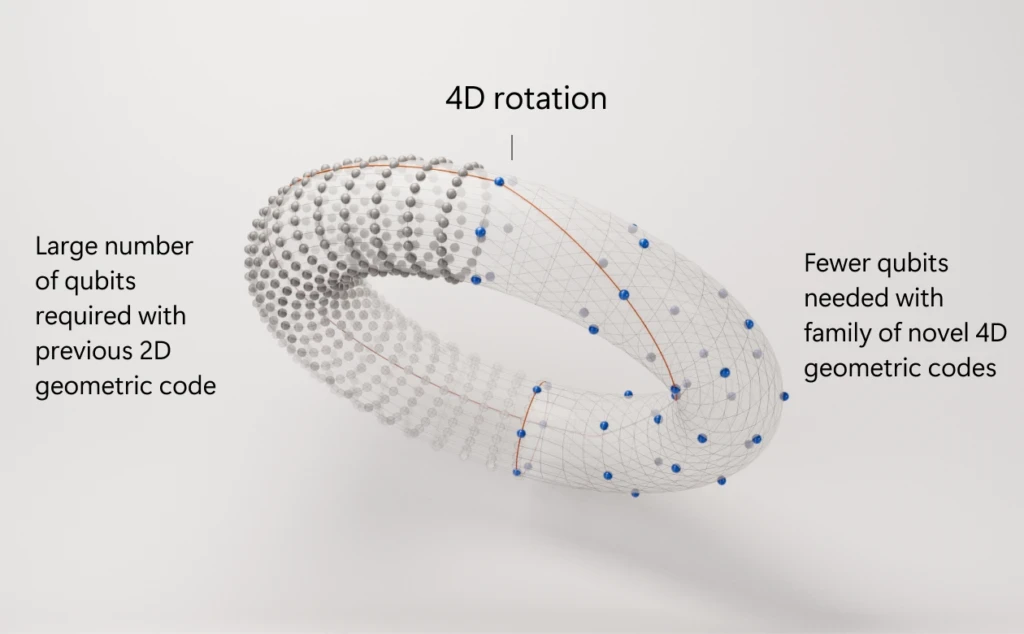
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors


How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack


IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer


Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence


Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025


Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing


Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’


IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
How Post-Quantum Cryptography Could Have Helped Prevent the $44M CoinDCX Hack

Bank of America: Quantum Computing Might Be Humanity’s Greatest Breakthrough Since Fire

Microsoft and Denmark Set Ambitious Goal: Hosting the World’s Most Powerful Quantum Computer with “Magne”
Quantum-Safe Surge: 70% of Billion-Dollar Enterprises Are Early Adopters, Says Capgemini Report

Texas Quantum Initiative Passes: Lone Star State Bids to Become Quantum Powerhouse

Europe’s Quantum Surge: Bridging the Private Funding Gap for Tech Dominance

Racing the Quantum Threat: 5 Nations Compress Post-Quantum Cryptography Timelines
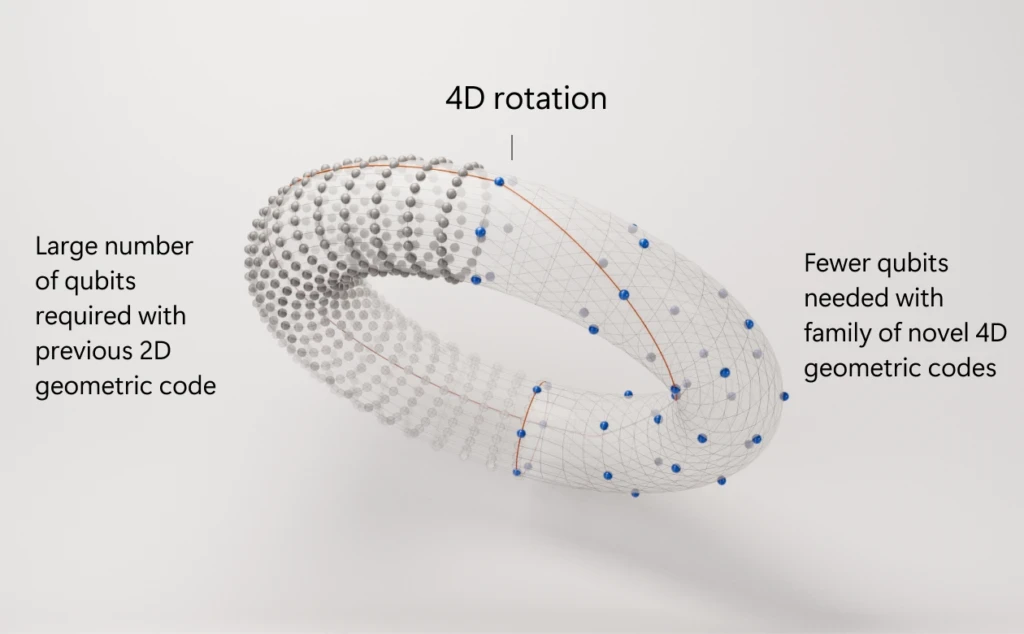
Microsoft’s Azure Quantum Unveils 4D Code Plan to Tame Quantum Errors

How Post‑Quantum Cryptography Could Have Stopped the $1.5 Billion Bybit Hack

IIT Delhi Achieves Quantum Breakthrough: Wireless Communication Over 1 Kilometer

Caltech Scientists Achieve Hyper-Entanglement in Atomic Motion: A Quantum Leap in Control and Coherence

Quantum Boom: Surge in Tech Deals & Funding Marks a Turning Point in 2025

Pasqal Charts Bold Course: Roadmap to 10,000 Qubits and Fault-Tolerant Quantum Computing

Quantum at a Turning Point: Nvidia CEO Declares Industry at ‘Inflection Point’

IBM Unveils Next-Generation Quantum Processor, Ushering In a New Era of Computation
Last week, Craig Gidney from Google Quantum AI published a breakthrough study that redefines the landscape of cryptographic security. His paper, “How to factor 2048 bit RSA integers with less than a million noisy qubits”, dramatically lowers the estimated quantum resources needed to break RSA-2048—one of the most widely used encryption standards securing everything from email to financial transactions to government databases.
Where previous estimates (including Gidney’s own 2019 study) projected that cracking RSA-2048 would require around 20 million qubits and 8 hours of computation, the new analysis reveals that it could be done in under a week using fewer than 1 million noisy qubits. This reduction of more than 95% in hardware requirements is a seismic shift in the projected timeline for “Q-Day”—the hypothetical moment when quantum computers can break modern encryption.
Read QuantumGenie's other industry insights.
What Makes RSA-2048 Vulnerable?
RSA encryption is based on the mathematical challenge of factoring large numbers into their prime components—a task that classical computers find prohibitively difficult at the 2048-bit level. This difficulty forms the backbone of digital security protocols used in secure web browsing (HTTPS), email encryption (PGP), VPNs, and many blockchain systems.
Quantum computers, however, can use Shor’s algorithm to factor these numbers exponentially faster. The catch? That algorithm requires high-fidelity quantum gates, large-scale error correction, and millions of qubits—until now.
Google’s Innovation: Shrinking the Qubit Budget
Gidney’s 2025 paper showcases several technical innovations that slash the qubit requirements for factoring RSA-2048:
Approximate Residue Arithmetic: This method, recently introduced by Chevignard, Fouque, and Schrottenloher (2024), streamlines modular arithmetic and reduces the depth of quantum circuits needed for number factoring.
Magic State Cultivation: A more space-efficient way of producing non-Clifford gate resources (known as magic states), crucial for enabling universal quantum computation under error correction.
Optimized Period Finding with Ekerå-Håstad Algorithms: These advanced number-theoretic optimizations allow for a more efficient implementation of the quantum part of Shor’s algorithm.
Yoked Surface Codes & Sparse Lookups: Techniques that minimize the overhead in fault-tolerant quantum circuits, enabling better scaling.
Collectively, these improvements reduce the physical qubit requirement to under 1 million and allow the algorithm to complete in less than 7 days, given favorable assumptions like a 0.1% gate error rate and a 1-microsecond surface code cycle time.
This represents a ~20x reduction in required qubits and vastly improves the practical feasibility of quantum attacks on RSA.
Read QuantumGenie's other industry insights.
Implications for Cryptographic Security
The broader takeaway is stark: RSA-2048 is no longer as safe as once believed.
While building a quantum computer capable of executing this attack is still a monumental engineering challenge, the new resource estimates bring that future much closer. If quantum hardware continues to progress as expected—with leading players like IBM, Google, and startups like Quantinuum and PsiQuantum scaling up both qubit numbers and error rates—Q-Day could realistically occur within 10 to 15 years, or sooner in a best-case scenario.
That means data encrypted today could be vulnerable tomorrow—especially for governments, banks, healthcare institutions, and cloud service providers that store data with long-term confidentiality requirements.
This underscores the risk of “harvest now, decrypt later” attacks, in which threat actors (including nation-states) are believed to be storing encrypted traffic now, anticipating that they’ll be able to decrypt it once quantum systems mature.
Read QuantumGenie's other industry insights.
Urgency for Post-Quantum Cryptography (PQC)
The cryptographic community has been preparing for this scenario for several years. The National Institute of Standards and Technology (NIST) has already finalized the first suite of post-quantum encryption standards, including lattice-based algorithms like CRYSTALS-Kyber and Dilithium, which are believed to be resistant to quantum attacks.
Yet, many systems—particularly in legacy environments—still depend on RSA-2048 or similar classical algorithms. Migrating these systems takes time, and in some cases, the encrypted data will need to remain secure for decades. That’s why Gidney’s paper acts as both a technical milestone and a public warning.
Organizations must start:
Inventorying existing cryptographic systems and identifying where RSA is used.
Deploying hybrid encryption (combining classical and quantum-resistant algorithms).
Adopting crypto-agility strategies to enable rapid algorithm updates in the future.
Educating stakeholders and regulators about the urgency of quantum readiness.
Read QuantumGenie's other industry insights.
Conclusion: The Countdown Is Real
Google’s 2025 quantum factoring estimate is more than a mathematical triumph—it’s a wake-up call. RSA-2048 has long been considered a gold standard in security, but this research makes clear that its lifespan is rapidly approaching an end.
The clock is ticking. And for the cybersecurity world, there’s no time to waste.
Reference:
Gidney, C. (2025). How to factor 2048 bit RSA integers with less than a million noisy qubits. Google Quantum AI. arXiv:2505.15917.
Need help evaluating your organization’s quantum risk exposure or building a migration roadmap? I can help design a tailored post-quantum strategy.
Let's talk!
Office:
1535 Broadway
New York, NY 10036
USA
Local time:
19:29:17
Let's talk!
Office:
1535 Broadway
New York, NY 10036
USA
Local time:
19:29:17
